Display Options
1601524362
Q !!Hs1Jq13jV6 09/30/2020 23:52:42 ID: 376386
8kun/qresearch: 10864489Q Clock [ Min: 8 | :25/:55 Mir: 42 | 180 Mir: 38 | :35/:05 Mir: 2 ]
Delta to Reply: 0 D_00:09:19 (seconds total: 559) (19) (1)
Epoch: 1601523803 (29) (2)
Anonymous 09/30/2020 23:43:23 ID:39774c 8kun/qresearch: 10864305

100%
Image Name: 09302020nyt1.png
Filename: 08e41859ca2515db376999299074104a284701075e774fa4c4ab36b1ebe9d5d8.png
EXIF DATA
name : 08e41859ca2515db376999299074104a284701075e774fa4c4ab36b1ebe9d5d8.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 778
geometry.height : 840
geometry.x : 0
geometry.y : 0
resolution.x : 37.79
resolution.y : 37.79
printSize.x : 20.5875
printSize.y : 22.2281
units : PixelsPerCentimeter
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 653520
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 778
pageGeometry.height : 840
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 2
properties.png:IHDR.color_type : 2 (Truecolor)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 778, 840
properties.png:pHYs : x_res=3779, y_res=3779, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : 2c0533a5e71f307436e7c862d15daed7f25746a0d1a17863376c4c1482159968
tainted :
filesize : 490960
numberPixels : 653520
filename : 08e41859ca2515db376999299074104a284701075e774fa4c4ab36b1ebe9d5d8.png
name : 08e41859ca2515db376999299074104a284701075e774fa4c4ab36b1ebe9d5d8.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 778
geometry.height : 840
geometry.x : 0
geometry.y : 0
resolution.x : 37.79
resolution.y : 37.79
printSize.x : 20.5875
printSize.y : 22.2281
units : PixelsPerCentimeter
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 653520
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 778
pageGeometry.height : 840
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 2
properties.png:IHDR.color_type : 2 (Truecolor)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 778, 840
properties.png:pHYs : x_res=3779, y_res=3779, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : 2c0533a5e71f307436e7c862d15daed7f25746a0d1a17863376c4c1482159968
tainted :
filesize : 490960
numberPixels : 653520
filename : 08e41859ca2515db376999299074104a284701075e774fa4c4ab36b1ebe9d5d8.png
Rebuffed by Vatican, Pompeo Assails China and Aligns
With Pope’s Critics
Pope Francis declined to see Secretary of State Mike Pompeo, who is demanding a harder Vatican line on China. The Holy See said meeting just before a U.S. election would be inappropriate.
By Jason Horowitz and Lara Jakes
Sept. 30, 2020, 7:26 p.m. ET
ROME — Secretary of State Mike Pompeo recently published a sharp letter excoriating the Vatican’s plans to renew an agreement with the Chinese government on Church operations in China. He promoted the article in a tweet, concluding, “The Vatican endangers its moral authority, should it renew the deal.”
An indignant Vatican took the article more as a calculated affront than a diplomatic gesture. The friction broke into the open on Wednesday as Mr. Pompeo arrived in Rome and met with prelates and others who are hostile to Pope Francis, while the Vatican denied him a meeting with the pontiff and rebuffed his efforts to derail the deal with China.
“Pompeo asked to meet” the pope, who turned him down because Francis had “clearly said that he does not receive political figures ahead of the elections,” Cardinal Pietro Parolin, who, as secretary of state, is the Vatican’s second-ranking official, told reporters.
But to some observers on both sides of the tensions between the Roman Catholic Church and the Trump administration, Mr. Pompeo’s visit is as much about the coming presidential election as about China policy. Mr. Pompeo dismissed that suggestion as absurd, but intended or not, his trip signals that President Trump is on the side of those conservative American Catholics who worry about the church’s direction under Francis and think he is soft on China.
Francis and Mr. Trump, who have exchanged sharp words in the past, present starkly different visions on issues ranging from the environment to immigration to the threat of populism. In appealing to the Vatican’s support for religious freedom as a reason to drop its China agreement, Mr. Pompeo seemed to seek common ground, but in a way that upset the pope’s chief allies and delighted his chief critics.
Cardinal Parolin said Mr. Pompeo’s article had caused “surprise” at the Vatican, because this visit to Rome by the secretary and the meetings with high officials at the Holy See had already been in the works and would have been a “more opportune” forum for airing grievances. He added that Mr. Pompeo’s choice to publish in First Things, a conservative Christian magazine that has called Francis a failure as Pope, also mattered.
https://www.nytimes.com/2020/09/30/world/europe/pompeo-pope-francis-china.html
With Pope’s Critics
Pope Francis declined to see Secretary of State Mike Pompeo, who is demanding a harder Vatican line on China. The Holy See said meeting just before a U.S. election would be inappropriate.
By Jason Horowitz and Lara Jakes
Sept. 30, 2020, 7:26 p.m. ET
ROME — Secretary of State Mike Pompeo recently published a sharp letter excoriating the Vatican’s plans to renew an agreement with the Chinese government on Church operations in China. He promoted the article in a tweet, concluding, “The Vatican endangers its moral authority, should it renew the deal.”
An indignant Vatican took the article more as a calculated affront than a diplomatic gesture. The friction broke into the open on Wednesday as Mr. Pompeo arrived in Rome and met with prelates and others who are hostile to Pope Francis, while the Vatican denied him a meeting with the pontiff and rebuffed his efforts to derail the deal with China.
“Pompeo asked to meet” the pope, who turned him down because Francis had “clearly said that he does not receive political figures ahead of the elections,” Cardinal Pietro Parolin, who, as secretary of state, is the Vatican’s second-ranking official, told reporters.
But to some observers on both sides of the tensions between the Roman Catholic Church and the Trump administration, Mr. Pompeo’s visit is as much about the coming presidential election as about China policy. Mr. Pompeo dismissed that suggestion as absurd, but intended or not, his trip signals that President Trump is on the side of those conservative American Catholics who worry about the church’s direction under Francis and think he is soft on China.
Francis and Mr. Trump, who have exchanged sharp words in the past, present starkly different visions on issues ranging from the environment to immigration to the threat of populism. In appealing to the Vatican’s support for religious freedom as a reason to drop its China agreement, Mr. Pompeo seemed to seek common ground, but in a way that upset the pope’s chief allies and delighted his chief critics.
Cardinal Parolin said Mr. Pompeo’s article had caused “surprise” at the Vatican, because this visit to Rome by the secretary and the meetings with high officials at the Holy See had already been in the works and would have been a “more opportune” forum for airing grievances. He added that Mr. Pompeo’s choice to publish in First Things, a conservative Christian magazine that has called Francis a failure as Pope, also mattered.
https://www.nytimes.com/2020/09/30/world/europe/pompeo-pope-francis-china.html
Image Search Tags: Mike Pompeo with mask on
>>10864305
When does a Church become a playground?
When does a Church become a business?
When does a Church become political?
When does a Church become corrupt?
When does a Church become willfully blind?
When does a Church become controlled?
Q
When does a Church become a playground?
When does a Church become a business?
When does a Church become political?
When does a Church become corrupt?
When does a Church become willfully blind?
When does a Church become controlled?
Q
Display Options
Delta to next: 236 D_10:38:22 (seconds total: 20428702) (25) (7)
Q !!Hs1Jq13jV6 02/07/2020 12:14:20 ID: 82fedb
8kun/qresearch: 8061906Q Clock [ Min: 12 | :25/:55 Mir: 38 | 180 Mir: 42 | :35/:05 Mir: 58 ]

Image Name: DzNz3avVsAEkayI.jpg
Filename: fcca4899ce921646b69d34f5d122cc72988665c8d14c2c071b0969ec80556f24.jpg
EXIF DATA
name : fcca4899ce921646b69d34f5d122cc72988665c8d14c2c071b0969ec80556f24.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 604
geometry.height : 1200
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 724800
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 604
pageGeometry.height : 1200
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 73be158545773f9b16c819deeb7e04e3179f04c399b5d27f93bdb4d3cacbac99
profiles.icc :
tainted :
filesize : 155514
numberPixels : 724800
filename : fcca4899ce921646b69d34f5d122cc72988665c8d14c2c071b0969ec80556f24.jpg
name : fcca4899ce921646b69d34f5d122cc72988665c8d14c2c071b0969ec80556f24.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 604
geometry.height : 1200
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 724800
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 604
pageGeometry.height : 1200
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 73be158545773f9b16c819deeb7e04e3179f04c399b5d27f93bdb4d3cacbac99
profiles.icc :
tainted :
filesize : 155514
numberPixels : 724800
filename : fcca4899ce921646b69d34f5d122cc72988665c8d14c2c071b0969ec80556f24.jpg
Image Search Tags: drop 2697
https://twitter.com/M2Madness/status/1225606976912199680
If dirty cops ran the investigation into the DNC breach, could an argument be made that it was corrupt?
If dirty cops ran the investigation into election interference, could an argument be made that it was corrupt?
If dirty cops ran the investigation into [HRC] private server/email scandal, could an argument be made that it was corrupt?
RUSSIA DID NOT 'HACK' [penetrate] THE DNC SERVER.
>internal DL / release
>crowdstrike manipulation of source
RUSSIA DID NOT INTERFERE WITH US ELECTION OF 2016.
>crowdstrike manipulation of source
The truth will be made public.
Q
If dirty cops ran the investigation into the DNC breach, could an argument be made that it was corrupt?
If dirty cops ran the investigation into election interference, could an argument be made that it was corrupt?
If dirty cops ran the investigation into [HRC] private server/email scandal, could an argument be made that it was corrupt?
RUSSIA DID NOT 'HACK' [penetrate] THE DNC SERVER.
>internal DL / release
>crowdstrike manipulation of source
RUSSIA DID NOT INTERFERE WITH US ELECTION OF 2016.
>crowdstrike manipulation of source
The truth will be made public.
Q
Display Options
Delta to next: 16 D_21:49:04 (seconds total: 1460944) (28) (1)
Q !!Hs1Jq13jV6 01/21/2020 14:25:16 ID: aa5bcf
8kun/qresearch: 7867006Q Clock [ Min: 55 | :25/:55 Mir: 55 | 180 Mir: 25 | :35/:05 Mir: 15 ]
Delta to Reply: 0 D_00:02:40 (seconds total: 160) (7) (7)
Epoch: 1579634556 (51) (6)
Anonymous 01/21/2020 14:22:36 ID:96d735 8kun/qresearch: 7866980
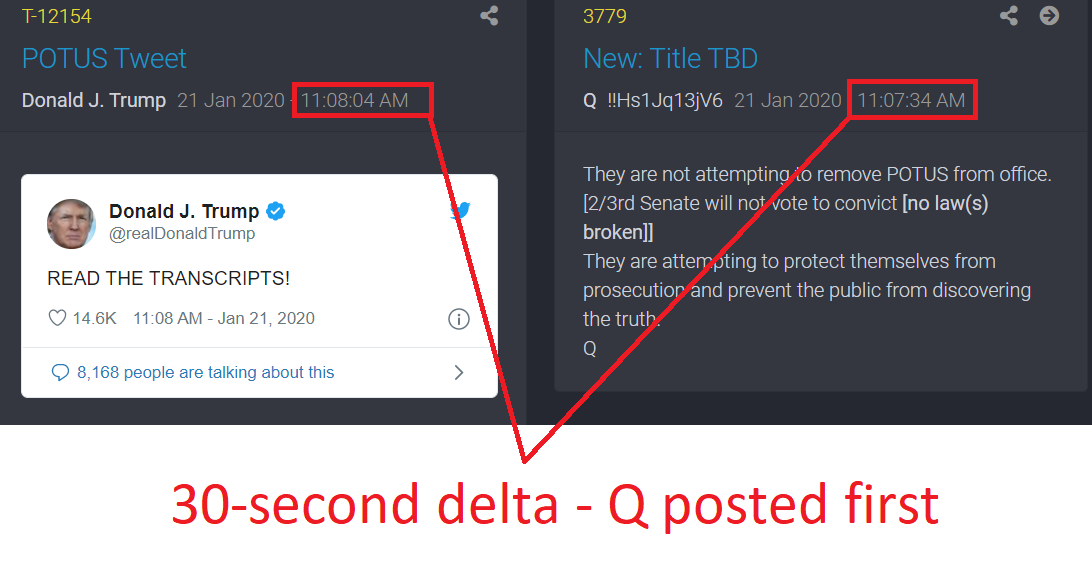
Image Name: 30 second delta.png
Filename: 12a7a4219b20f7b54378d1706a4ce25355f8f866e28b282b2053ce1ebe57e8fe.png
EXIF DATA
name : 12a7a4219b20f7b54378d1706a4ce25355f8f866e28b282b2053ce1ebe57e8fe.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 1092
geometry.height : 576
geometry.x : 0
geometry.y : 0
resolution.x : 47.24
resolution.y : 47.24
printSize.x : 23.116
printSize.y : 12.1931
units : PixelsPerCentimeter
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 628992
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1092
pageGeometry.height : 576
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 2
properties.png:IHDR.color_type : 2 (Truecolor)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 1092, 576
properties.png:pHYs : x_res=4724, y_res=4724, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : 96f6f50ea51cef79d716ca62019cadad3891be27e4b6c5cadea2bc4e025069de
tainted :
filesize : 57819
numberPixels : 628992
filename : 12a7a4219b20f7b54378d1706a4ce25355f8f866e28b282b2053ce1ebe57e8fe.png
name : 12a7a4219b20f7b54378d1706a4ce25355f8f866e28b282b2053ce1ebe57e8fe.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 1092
geometry.height : 576
geometry.x : 0
geometry.y : 0
resolution.x : 47.24
resolution.y : 47.24
printSize.x : 23.116
printSize.y : 12.1931
units : PixelsPerCentimeter
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 628992
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1092
pageGeometry.height : 576
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 2
properties.png:IHDR.color_type : 2 (Truecolor)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 1092, 576
properties.png:pHYs : x_res=4724, y_res=4724, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : 96f6f50ea51cef79d716ca62019cadad3891be27e4b6c5cadea2bc4e025069de
tainted :
filesize : 57819
numberPixels : 628992
filename : 12a7a4219b20f7b54378d1706a4ce25355f8f866e28b282b2053ce1ebe57e8fe.png
>>7866867
Image Search Tags: qproof q proof confirmed 30s 30 second delay
>>7866980
Thank you, Anon.
[SEC] server re-routes create delays.
[F]
Q
Thank you, Anon.
[SEC] server re-routes create delays.
[F]
Q
Display Options
Delta to next: 24 D_00:54:47 (seconds total: 2076887) (38) (2)
Q !!Hs1Jq13jV6 12/28/2019 13:30:29 ID: 2b1500
8kun/qresearch: 7643985Q Clock [ Min: 31 | :25/:55 Mir: 19 | 180 Mir: 1 | :35/:05 Mir: 39 ]
Delta to Reply: 0 D_00:01:46 (seconds total: 106) (7) (7)
Epoch: 1577557723 (49) (4)
Anonymous 12/28/2019 13:28:43 ID:b8b53b 8kun/qresearch: 7643939
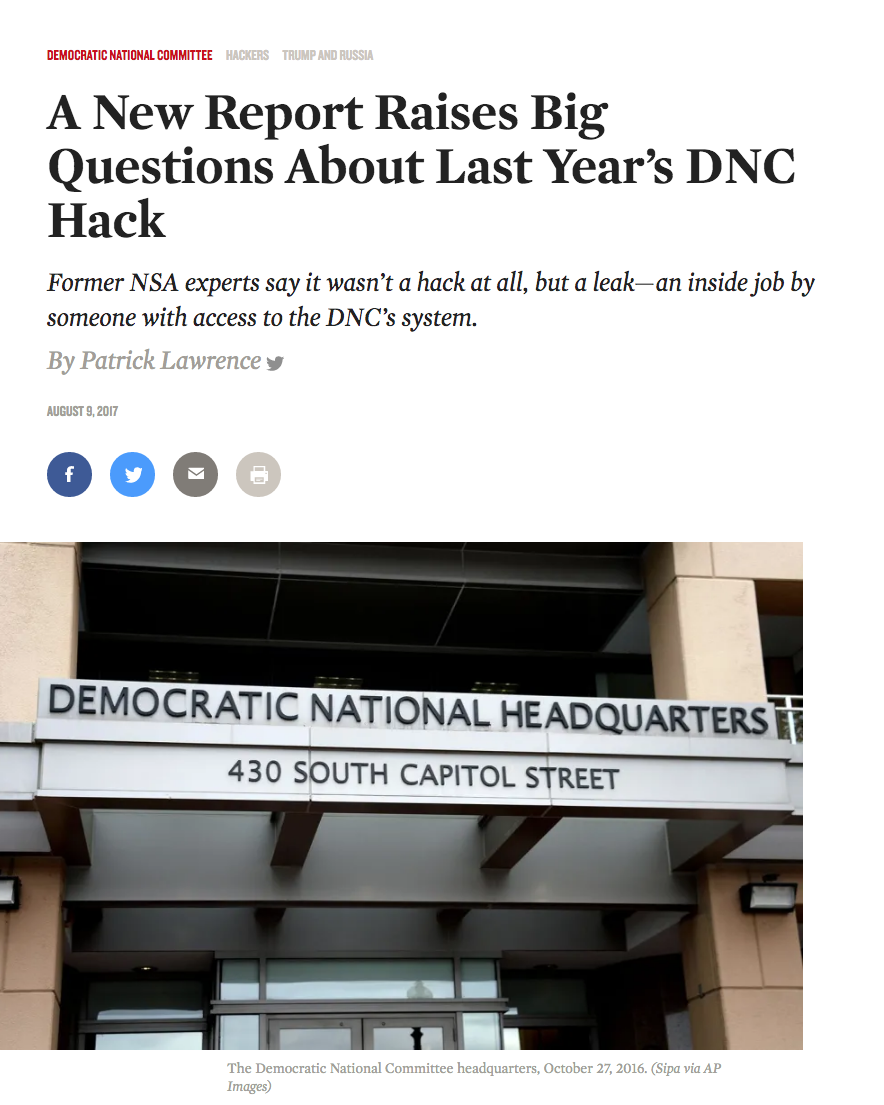
Image Name: Screen Shot 2019-12-28 at 19.28.12.png
Filename: 652133b0cebd48699b11c279c83891eceee037d27b71f3c8e89a2ddfe36a4c78.png
EXIF DATA
name : 652133b0cebd48699b11c279c83891eceee037d27b71f3c8e89a2ddfe36a4c78.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 884
geometry.height : 1105
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColorAlpha
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.alpha : 1
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 976820
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFFFF
borderColor : #DFDFDFFF
matteColor : #BDBDBDFF
transparentColor : #00000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 884
pageGeometry.height : 1105
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2019
properties.icc:description : Display
properties.png:iCCP : chunk was found
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 6
properties.png:IHDR.color_type : 6 (RGBA)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 884, 1105
properties.signature : a862058f23970ed5a10b1e5ed0c3c60e96d22022f325cf629d119b8e052c94e9
profiles.icc :
tainted :
filesize : 526387
numberPixels : 976820
filename : 652133b0cebd48699b11c279c83891eceee037d27b71f3c8e89a2ddfe36a4c78.png
name : 652133b0cebd48699b11c279c83891eceee037d27b71f3c8e89a2ddfe36a4c78.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 884
geometry.height : 1105
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColorAlpha
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.alpha : 1
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 976820
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFFFF
borderColor : #DFDFDFFF
matteColor : #BDBDBDFF
transparentColor : #00000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 884
pageGeometry.height : 1105
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2019
properties.icc:description : Display
properties.png:iCCP : chunk was found
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 6
properties.png:IHDR.color_type : 6 (RGBA)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 884, 1105
properties.signature : a862058f23970ed5a10b1e5ed0c3c60e96d22022f325cf629d119b8e052c94e9
profiles.icc :
tainted :
filesize : 526387
numberPixels : 976820
filename : 652133b0cebd48699b11c279c83891eceee037d27b71f3c8e89a2ddfe36a4c78.png
>>7643842
orensicator’s first decisive findings, made public in the paper dated July 9, concerned the volume of the supposedly hacked material and what is called the transfer rate—the time a remote hack would require. The metadata established several facts in this regard with granular precision: On the evening of July 5, 2016, 1,976 megabytes of data were downloaded from the DNC’s server. The operation took 87 seconds. This yields a transfer rate of 22.7 megabytes per second.
These statistics are matters of record and essential to disproving the hack theory. No Internet service provider, such as a hacker would have had to use in mid-2016, was capable of downloading data at this speed. Compounding this contradiction, Guccifer claimed to have run his hack from Romania, which, for numerous reasons technically called delivery overheads, would slow down the speed of a hack even further from maximum achievable speeds.
https://www.thenation.com/article/a-new-report-raises-big-questions-about-last-years-dnc-hack/
orensicator’s first decisive findings, made public in the paper dated July 9, concerned the volume of the supposedly hacked material and what is called the transfer rate—the time a remote hack would require. The metadata established several facts in this regard with granular precision: On the evening of July 5, 2016, 1,976 megabytes of data were downloaded from the DNC’s server. The operation took 87 seconds. This yields a transfer rate of 22.7 megabytes per second.
These statistics are matters of record and essential to disproving the hack theory. No Internet service provider, such as a hacker would have had to use in mid-2016, was capable of downloading data at this speed. Compounding this contradiction, Guccifer claimed to have run his hack from Romania, which, for numerous reasons technically called delivery overheads, would slow down the speed of a hack even further from maximum achievable speeds.
https://www.thenation.com/article/a-new-report-raises-big-questions-about-last-years-dnc-hack/
Image Search Tags: dnc hack news article
>>7643939
Display Options
Delta to next: 0 D_00:07:02 (seconds total: 422) (8) (8)
Q !!Hs1Jq13jV6 12/28/2019 13:23:27 ID: 2b1500
8kun/qresearch: 7643842Q Clock [ Min: 31 | :25/:55 Mir: 19 | 180 Mir: 1 | :35/:05 Mir: 39 ]
DNC server(s).
Crowdstrike.
Did Russia 'break-in' to DNC server(s)?
Why did FBI accept 'indirect' evidence re: DNC server(s) 'hack''break-in' by Crowdstrike [Ukraine]?
Why didn't FBI 'directly' investigate DNC server(s) [in-hand]?
Download speed internal data DL vs remote? [1]
https://www.realclearpolitics.com/video/2017/01/02/assange_to_hannity_our_source_was_not_the_russian_government.html
[1]
How does one provide content to WL?
>comp-to-comp
>person-to-person [1]
Personal comms [secured] prior to release? [1]
The (Source(s)):
>Feeder [1]
>Recipient [1]
Interning for the DNC can be deadly.
Does Crowdstrike possess 'gov_capablity' to trace 'break-in' route(s)?
Does Crowdstrike possess 'gov_capability' re: foreign intercepts?
Possible to layer/insert code [Crowdstrike] to designate intruder [intended target]?
NSA data_bridge DNC-Crowdstrike [bulk data collection]
Matters of National Security [Highest Levels].
FISA is only the beginning.
The hole is DEEP.
Q
Crowdstrike.
Did Russia 'break-in' to DNC server(s)?
Why did FBI accept 'indirect' evidence re: DNC server(s) 'hack''break-in' by Crowdstrike [Ukraine]?
Why didn't FBI 'directly' investigate DNC server(s) [in-hand]?
Download speed internal data DL vs remote? [1]
https://www.realclearpolitics.com/video/2017/01/02/assange_to_hannity_our_source_was_not_the_russian_government.html
[1]
How does one provide content to WL?
>comp-to-comp
>person-to-person [1]
Personal comms [secured] prior to release? [1]
The (Source(s)):
>Feeder [1]
>Recipient [1]
Interning for the DNC can be deadly.
Does Crowdstrike possess 'gov_capablity' to trace 'break-in' route(s)?
Does Crowdstrike possess 'gov_capability' re: foreign intercepts?
Possible to layer/insert code [Crowdstrike] to designate intruder [intended target]?
NSA data_bridge DNC-Crowdstrike [bulk data collection]
Matters of National Security [Highest Levels].
FISA is only the beginning.
The hole is DEEP.
Q
Display Options
Delta to next: 32 D_20:52:42 (seconds total: 2839962) (39) (3)
Q !!mG7VJxZNCI 11/25/2019 16:30:45 ID: ac3c8c
8kun/qresearch: 7371947Q Clock [ Min: 58 | :25/:55 Mir: 52 | 180 Mir: 28 | :35/:05 Mir: 12 ]
[D]'s (internal) infiltration issue(s) w/ protecting NAT SEC?
Deliberate?
Do you believe in coincidences?
>DF Chinese spy_insert 20+ years
https://www.usatoday.com/story/news/politics/onpolitics/2018/08/04/trump-russia-investigation-dianne-feinstein-chinese-spy/908865002/
>Awan IT scandal
https://www.foxnews.com/opinion/democrats-it-scandal-set-to-explode-with-possible-plea-deal
>Omar paid [F] agent
https://www.thegatewaypundit.com/2019/11/ilhan-omar-accused-of-being-a-paid-agent-of-qatar-and-accessing-sensitive-info-for-iran-court-testimony/
>Clinton server > China relay
https://gohmert.house.gov/news/documentsingle.aspx?DocumentID=398652
>[VJ] direct relay > Iran pre/post Iran deal [future marker]
>[Kerry] direct relay > Iran pre/post Iran deal [future marker]
IF KNOWN - WHY IS IT ALLOWED TO HAPPEN?
IF KNOWN - WILL THERE BE JUSTICE?
It's only a matter of time.
Q
Deliberate?
Do you believe in coincidences?
>DF Chinese spy_insert 20+ years
https://www.usatoday.com/story/news/politics/onpolitics/2018/08/04/trump-russia-investigation-dianne-feinstein-chinese-spy/908865002/
>Awan IT scandal
https://www.foxnews.com/opinion/democrats-it-scandal-set-to-explode-with-possible-plea-deal
>Omar paid [F] agent
https://www.thegatewaypundit.com/2019/11/ilhan-omar-accused-of-being-a-paid-agent-of-qatar-and-accessing-sensitive-info-for-iran-court-testimony/
>Clinton server > China relay
https://gohmert.house.gov/news/documentsingle.aspx?DocumentID=398652
>[VJ] direct relay > Iran pre/post Iran deal [future marker]
>[Kerry] direct relay > Iran pre/post Iran deal [future marker]
IF KNOWN - WHY IS IT ALLOWED TO HAPPEN?
IF KNOWN - WILL THERE BE JUSTICE?
It's only a matter of time.
Q
Display Options
Delta to next: 119 D_21:36:58 (seconds total: 10359418) (31) (4)
Q !!mG7VJxZNCI 07/28/2019 19:53:47 ID: 8442b9
8chan/qresearch: 7234526Q Clock [ Min: 58 | :25/:55 Mir: 52 | 180 Mir: 28 | :35/:05 Mir: 12 ]
The SWAMP runs deep.
DNC server(s) hold many answers.
SCARAMUCCI MODEL.
DNI & NSA
[AWAN]
[DWS]
[D_Congress]
House of Cards.
You didn't think the plea deal was the end did you?
Q
DNC server(s) hold many answers.
SCARAMUCCI MODEL.
DNI & NSA
[AWAN]
[DWS]
[D_Congress]
House of Cards.
You didn't think the plea deal was the end did you?
Q
Display Options
Delta to next: 122 D_05:48:15 (seconds total: 10561695) (33) (6)
Q!!mG7VJxZNCI 03/28/2019 14:05:32 ID: 87b5e7
8chan/qresearch: 5944492Q Clock [ Min: 56 | :25/:55 Mir: 54 | 180 Mir: 26 | :35/:05 Mir: 14 ]
Delta to Reply: 0 D_00:05:14 (seconds total: 314) (8) (8)
Epoch: 1553796018 (45) (9)
Anonymous 03/28/2019 14:00:18 ID:b4c212 8chan/qresearch: 5944351
>>5944119
SERVER DOWN Q
SERVER DOWN Q
>>5944351
What does that tell you about the size of the movement?
Q
What does that tell you about the size of the movement?
Q
Display Options
Delta to next: 13 D_20:48:06 (seconds total: 1198086) (33) (6)
Q!!mG7VJxZNCI 03/14/2019 17:17:26 ID: 12a111
8chan/qresearch: 5685074Q Clock [ Min: 42 | :25/:55 Mir: 8 | 180 Mir: 12 | :35/:05 Mir: 28 ]
https://seekingalpha.com/news/3442879-facebook-says-outage-caused-server-change-now-resolved
"Server config change."
Q
"Server config change."
Q
Display Options
Delta to next: 1 D_15:27:09 (seconds total: 142029) (18) (9)
Q!!mG7VJxZNCI 03/13/2019 01:50:17 ID: 6dd976
8chan/qresearch: 5655015Q Clock [ Min: 41 | :25/:55 Mir: 9 | 180 Mir: 11 | :35/:05 Mir: 29 ]
Delta to Reply: 0 D_00:02:02 (seconds total: 122) (5) (5)
Epoch: 1552456095 (42) (6)
Q !!mG7VJxZNCI03/13/2019 01:48:15 ID:6dd976 8chan/qresearch: 5654980
https://twitter.com/RepRatcliffe/status/1105658231198765057
The Tarmac Meeting.
Days Later….
[JC] "No charges are appropriate……….."
HOW DID HRC OBTAIN SAP (SPECIAL ACCESS PROGRAMS) ON HER PERSONAL SERVER(S)?
ACCESS TO SAP/SCI IS RECORDED IN A LOCAL ACCESS REGISTER OR IN A COMPUTER DATABASE —- WHERE ARE THE RECORDS?
IDEN OF 'SPECIFIC' SAP/SCI ON THE SERVER PROVIDES A TARGET (ROADMAP) TO REVIEW ACCESS LOGS TO THAT SPECIFIC PROGRAM?
WHAT PROCESS AND/OR SEC CLEARANCE WOULD BE REQ TO WALK-AWAY [TERMINAL_CLEAR] W/ SAP/SCI MATERIAL 'ELECTRONICALLY'?
Did a Foreign State gain access to the server?
Did a Foreign State gain access to the SAP/SCI material on the server?
https://thehill.com/policy/national-security/404192-fbi-denies-trump-claim-that-china-hacked-clintons-private-email
IF THE TOP FBI CHAIN OF COMMAND FOR THE MIDYEAR INVESTIGATION WERE *ALL* FIRED DOES ONE CONCLUDE THE INVESTIGATION WAS NOT CONDUCTED PROPERLY?
DOES ONE CONCLUDE ALL STATEMENTS MADE BY THE FBI (THINK NO HACK OF SERVER AS SINGLE EXAMPLE) COULD BE FALSE?
Take a moment and think about what that means.
[ ]
TREASON.
Q
The Tarmac Meeting.
Days Later….
[JC] "No charges are appropriate……….."
HOW DID HRC OBTAIN SAP (SPECIAL ACCESS PROGRAMS) ON HER PERSONAL SERVER(S)?
ACCESS TO SAP/SCI IS RECORDED IN A LOCAL ACCESS REGISTER OR IN A COMPUTER DATABASE —- WHERE ARE THE RECORDS?
IDEN OF 'SPECIFIC' SAP/SCI ON THE SERVER PROVIDES A TARGET (ROADMAP) TO REVIEW ACCESS LOGS TO THAT SPECIFIC PROGRAM?
WHAT PROCESS AND/OR SEC CLEARANCE WOULD BE REQ TO WALK-AWAY [TERMINAL_CLEAR] W/ SAP/SCI MATERIAL 'ELECTRONICALLY'?
Did a Foreign State gain access to the server?
Did a Foreign State gain access to the SAP/SCI material on the server?
https://thehill.com/policy/national-security/404192-fbi-denies-trump-claim-that-china-hacked-clintons-private-email
IF THE TOP FBI CHAIN OF COMMAND FOR THE MIDYEAR INVESTIGATION WERE *ALL* FIRED DOES ONE CONCLUDE THE INVESTIGATION WAS NOT CONDUCTED PROPERLY?
DOES ONE CONCLUDE ALL STATEMENTS MADE BY THE FBI (THINK NO HACK OF SERVER AS SINGLE EXAMPLE) COULD BE FALSE?
Take a moment and think about what that means.
[ ]
TREASON.
Q
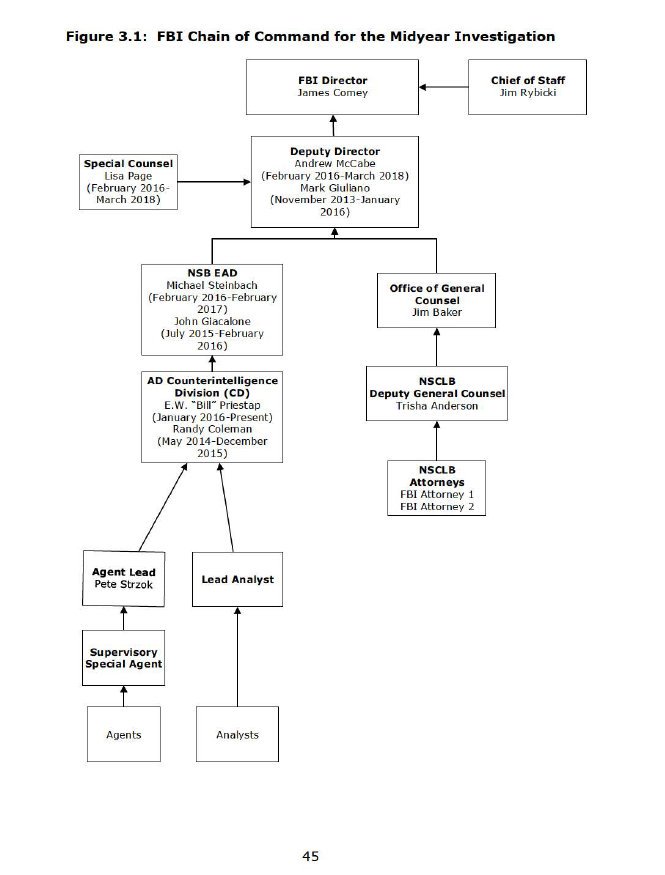
Image Name: DjsnjmeW0AAGXPH.jpg
Filename: d527cc879b23a4138cbf12bbc4b46860c8e68630b3eafee8e06304f4943b592f.jpg
EXIF DATA
name : d527cc879b23a4138cbf12bbc4b46860c8e68630b3eafee8e06304f4943b592f.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 665
geometry.height : 875
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 581875
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 665
pageGeometry.height : 875
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 735effe01e749ea00119ca876a0eda9cda820c0d2b9a7bcba7c79668f7798338
tainted :
filesize : 49151
numberPixels : 581875
filename : d527cc879b23a4138cbf12bbc4b46860c8e68630b3eafee8e06304f4943b592f.jpg
name : d527cc879b23a4138cbf12bbc4b46860c8e68630b3eafee8e06304f4943b592f.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 665
geometry.height : 875
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 581875
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 665
pageGeometry.height : 875
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 735effe01e749ea00119ca876a0eda9cda820c0d2b9a7bcba7c79668f7798338
tainted :
filesize : 49151
numberPixels : 581875
filename : d527cc879b23a4138cbf12bbc4b46860c8e68630b3eafee8e06304f4943b592f.jpg
Image Search Tags:
>>5654980
Display Options
Delta to next: 0 D_00:02:02 (seconds total: 122) (5) (5)
Q!!mG7VJxZNCI 03/13/2019 01:48:15 ID: 6dd976
8chan/qresearch: 5654980Q Clock [ Min: 41 | :25/:55 Mir: 9 | 180 Mir: 11 | :35/:05 Mir: 29 ]
https://twitter.com/RepRatcliffe/status/1105658231198765057
The Tarmac Meeting.
Days Later….
[JC] "No charges are appropriate……….."
HOW DID HRC OBTAIN SAP (SPECIAL ACCESS PROGRAMS) ON HER PERSONAL SERVER(S)?
ACCESS TO SAP/SCI IS RECORDED IN A LOCAL ACCESS REGISTER OR IN A COMPUTER DATABASE —- WHERE ARE THE RECORDS?
IDEN OF 'SPECIFIC' SAP/SCI ON THE SERVER PROVIDES A TARGET (ROADMAP) TO REVIEW ACCESS LOGS TO THAT SPECIFIC PROGRAM?
WHAT PROCESS AND/OR SEC CLEARANCE WOULD BE REQ TO WALK-AWAY [TERMINAL_CLEAR] W/ SAP/SCI MATERIAL 'ELECTRONICALLY'?
Did a Foreign State gain access to the server?
Did a Foreign State gain access to the SAP/SCI material on the server?
https://thehill.com/policy/national-security/404192-fbi-denies-trump-claim-that-china-hacked-clintons-private-email
IF THE TOP FBI CHAIN OF COMMAND FOR THE MIDYEAR INVESTIGATION WERE *ALL* FIRED DOES ONE CONCLUDE THE INVESTIGATION WAS NOT CONDUCTED PROPERLY?
DOES ONE CONCLUDE ALL STATEMENTS MADE BY THE FBI (THINK NO HACK OF SERVER AS SINGLE EXAMPLE) COULD BE FALSE?
Take a moment and think about what that means.
[ ]
TREASON.
Q
The Tarmac Meeting.
Days Later….
[JC] "No charges are appropriate……….."
HOW DID HRC OBTAIN SAP (SPECIAL ACCESS PROGRAMS) ON HER PERSONAL SERVER(S)?
ACCESS TO SAP/SCI IS RECORDED IN A LOCAL ACCESS REGISTER OR IN A COMPUTER DATABASE —- WHERE ARE THE RECORDS?
IDEN OF 'SPECIFIC' SAP/SCI ON THE SERVER PROVIDES A TARGET (ROADMAP) TO REVIEW ACCESS LOGS TO THAT SPECIFIC PROGRAM?
WHAT PROCESS AND/OR SEC CLEARANCE WOULD BE REQ TO WALK-AWAY [TERMINAL_CLEAR] W/ SAP/SCI MATERIAL 'ELECTRONICALLY'?
Did a Foreign State gain access to the server?
Did a Foreign State gain access to the SAP/SCI material on the server?
https://thehill.com/policy/national-security/404192-fbi-denies-trump-claim-that-china-hacked-clintons-private-email
IF THE TOP FBI CHAIN OF COMMAND FOR THE MIDYEAR INVESTIGATION WERE *ALL* FIRED DOES ONE CONCLUDE THE INVESTIGATION WAS NOT CONDUCTED PROPERLY?
DOES ONE CONCLUDE ALL STATEMENTS MADE BY THE FBI (THINK NO HACK OF SERVER AS SINGLE EXAMPLE) COULD BE FALSE?
Take a moment and think about what that means.
[ ]
TREASON.
Q
Display Options
Delta to next: 5 D_01:48:17 (seconds total: 438497) (35) (8)
Q!!mG7VJxZNCI 03/07/2019 22:59:58 ID: f9e971
8chan/qresearch: 5568629Q Clock [ Min: 35 | :25/:55 Mir: 15 | 180 Mir: 5 | :35/:05 Mir: 35 ]
Delta to Reply: 0 D_03:28:50 (seconds total: 12530) (11) (2)
Epoch: 1552005068 (32) (5)
Anonymous 03/07/2019 19:31:08 ID:9a6a8f 8chan/qresearch: 5565314
Keking out right now. Pretty sure I found something. Rip me apart if I’m wrong though. So many shills on here. You’re missing crumbs. Look here, not [here]. Responding to post 2996 Q says, “how is that possible for a ‘supposed’ non_gov entity?”
How is it possible that FB tracks data even when the app is deleted? In post 2993 (3/7/109) Q is calling out @Snowden. So I used the filter to find posts relating to WikiLeaks. Q’s post from July 31, 2018 is a screenshot of the Wikileaks Vault 7… released MARCH 7. Sounds confusing just trying to show you my thought process, stay with me, it makes sense.
“Unlike bullets, bombs or missiles, most CIA malware is designed to live for days or even years after it has reached its 'target'. CIA malware does not "explode on impact" but rather permanently infests its target. In order to infect target's device, copies of the malware must be placed on the target's devices, giving physical possession of the malware to the target. To exfiltrate data back to the CIA or to await further instructions the malware must communicate with CIA Command & Control (C2) systems placed on internet connected servers. But such servers are typically not approved to hold classified information, so CIA command and control systems are also made unclassified.” FROM VAULT 7
Links below that direct you to user forums on how to not leave a digital fingerprint that can be associated with the CIA, and how to construct an imitation fingerprint. Using Facebook as their ‘fingerprint’ they are able to install malware on peoples’ phones, tablets, and computers which relay all data back to a central server using HIVE.
I suggest all anons who have given up life to research this shit like me should read this document to completion.
I noticed the enormous amount of comparisons between “packets of data” and “bombs”, dunno why probably just autistic. I looked back in the Qmap and on March 5, 2019 an anon posted how London Police “called them bombs not suspicious packages” Q responds in 2974 with “Fire”.
I went into Vault 7 Projects, search for “fire”….
“Angelfire is an implant comprised of five components: Solartime, Wolfcreek, Keystone (previously MagicWand), BadMFS, and the Windows Transitory File system”
FUCKING KEYSTONE KEK
“Keystone is part of the Wolfcreek implant and responsible for starting malicious user applications. Loaded implants never touch the file system, so there is very little forensic evidence that the process was ever ran.” This makes post Q 381 much easier to understand
“We Won’t telegraph our moves to the ENEMY.
We will however light a FIRE to flush them out.”
Q
Q is saying that they are using the Anglefire to predict the Deep State’s moves without being detected. In the user files it says a key must be used to open magicwand (keystone). In Q post 270 he says that ADM R/NSA (W&W) + POTUS/USMIL = Apply the Keystone. Paint the Picture. In post 167 Q says POTUS opened the door of all doors. Expand your thinking. What is the keystone? Now this could be confirmation bias but based off of what we just read we can now infer that Q was saying trump gave Admiral Rogers permission to use Keystone and Activate malware in order to collect data on DS. Furthermore who uses a magicwand? A wizard. (W&W)
How is it possible that FB tracks data even when the app is deleted? In post 2993 (3/7/109) Q is calling out @Snowden. So I used the filter to find posts relating to WikiLeaks. Q’s post from July 31, 2018 is a screenshot of the Wikileaks Vault 7… released MARCH 7. Sounds confusing just trying to show you my thought process, stay with me, it makes sense.
“Unlike bullets, bombs or missiles, most CIA malware is designed to live for days or even years after it has reached its 'target'. CIA malware does not "explode on impact" but rather permanently infests its target. In order to infect target's device, copies of the malware must be placed on the target's devices, giving physical possession of the malware to the target. To exfiltrate data back to the CIA or to await further instructions the malware must communicate with CIA Command & Control (C2) systems placed on internet connected servers. But such servers are typically not approved to hold classified information, so CIA command and control systems are also made unclassified.” FROM VAULT 7
Links below that direct you to user forums on how to not leave a digital fingerprint that can be associated with the CIA, and how to construct an imitation fingerprint. Using Facebook as their ‘fingerprint’ they are able to install malware on peoples’ phones, tablets, and computers which relay all data back to a central server using HIVE.
I suggest all anons who have given up life to research this shit like me should read this document to completion.
I noticed the enormous amount of comparisons between “packets of data” and “bombs”, dunno why probably just autistic. I looked back in the Qmap and on March 5, 2019 an anon posted how London Police “called them bombs not suspicious packages” Q responds in 2974 with “Fire”.
I went into Vault 7 Projects, search for “fire”….
“Angelfire is an implant comprised of five components: Solartime, Wolfcreek, Keystone (previously MagicWand), BadMFS, and the Windows Transitory File system”
FUCKING KEYSTONE KEK
“Keystone is part of the Wolfcreek implant and responsible for starting malicious user applications. Loaded implants never touch the file system, so there is very little forensic evidence that the process was ever ran.” This makes post Q 381 much easier to understand
“We Won’t telegraph our moves to the ENEMY.
We will however light a FIRE to flush them out.”
Q
Q is saying that they are using the Anglefire to predict the Deep State’s moves without being detected. In the user files it says a key must be used to open magicwand (keystone). In Q post 270 he says that ADM R/NSA (W&W) + POTUS/USMIL = Apply the Keystone. Paint the Picture. In post 167 Q says POTUS opened the door of all doors. Expand your thinking. What is the keystone? Now this could be confirmation bias but based off of what we just read we can now infer that Q was saying trump gave Admiral Rogers permission to use Keystone and Activate malware in order to collect data on DS. Furthermore who uses a magicwand? A wizard. (W&W)
>>5565314 (/pb)
Something you should explore further.
Impressive, most impressive.
Q
Something you should explore further.
Impressive, most impressive.
Q
Display Options
Delta to next: 1 D_05:05:40 (seconds total: 104740) (16) (7)
Q!!mG7VJxZNCI 03/06/2019 17:54:18 ID: 5b3d8f
8chan/qresearch: 5543889Q Clock [ Min: 34 | :25/:55 Mir: 16 | 180 Mir: 4 | :35/:05 Mir: 36 ]
FB RETURNING TO THE NEWS.
LIFELOG (DARPA) ENDS > FB BEGINS
LIFELOG (DARPA) TEAM TRANSFER > FB
WHAT (DARPA) TEAM MEMBERS PAST/PRESENT WORK FOR FB?
WHAT DIVISIONS?
LOCATE (3) PUBLIC.
(9) TOTAL (6_NON PUB).
BUILDING 8 EXPOSED (HERE) WHEN?
[4-11-18]
*THINK SCRAMBLE [OFFLINE SCRUB] POST XBOX/PS CHAT LOGS DROP*
[MS SHUTDOWN IMMEDIATELY POST DROP]
BUILDING 8 NEWS RELEASE "RESTRUCTURING BUILDING 8" RELEASE?
[12-14-18] > RIP
https://techcrunch.com/2018/12/14/facebook-restructures-building-8-separating-projects-into-reality-labs-and-portal-groups/
RIP = FALSE
REORG = TRUE
CHINA-CHINA-CHINA
CHINA-CHINA-CHINA
[OPEN ACCESS - PAY FOR PLAY]
LAWS WHICH PREVENT C_A OPERATIONS INSIDE HOMELAND?
BULK DATA COLLECTION_NSA_HOMELAND?
BULK DATA COLLECTION_C_A_HOMELAND?
HOW DOES THE C_A AVOID LAW TRIGGER RE: UMBRELLA_SPY_HOMELAND?
FACEBOOK [CHINA_BUILDING 8]
GOOGLE [CHINA_DRAGONFLY]
TWITTER [US_LEG_TRACK]
FACEBOOK TRACK USER GPS, VOICE & TEXT?
GOOGLE TRACK USER GPS, VOICE & TEXT?
TWITTER TRACK USER GPS?
[PHONE_PAD_MICROPHONE_ALGO_EMBED]
ALL FOR MARKETING PURPOSES AS PUBLICLY DISCLOSED?
WHO HAS ACCESS TO BULK TRACK DATA?
WHO HAS ACCESS TO BULK DATA?
IF NSA HAS ABILITY TO 'ABSORB' DATA STREAM UT IN-HOUSE TOOLS, DOES C_A HAVE ABILITY TO 'COLLECT' DATA STREAM FROM 'FUNDED''NETWORKED' OFFSHOOTS [BIG TECH]?
OFFSHOOTS NECESSARY TO AVOID C_A BREACH OF US DOMESTIC LAW?
AMAZON SERVER/CLOUD CONTRACT?
AMAZON_SERVER/CLOUD_ROUTE_DATA 1-99 DOMESTIC?
C_A TASKED W/ GATHERING AND ANALYZING INFO ON FOREIGN GOVS + INDIVS? SIGINT - COV
NSA TASKED W/ GATHERING AND ANALYZING INFO ON A GLOBAL SCALE (INCLUDING DOMESTIC)? SIGINT - COV
WHAT FORMER US PRESIDENT WAS C_A DIRECTOR?
http://www.thedrive.com/the-war-zone/25241/george-h-w-bush-saved-the-cia
THINK C_A [BRENNAN] AUTH SPY CAMPAIGN US SENATE UNDER HUSSEIN.
THINK C_A INSTALL CAMPAIGN US HOUSE & SENATE INFILTRATION.
[PART 1 OF 9]
Q
LIFELOG (DARPA) ENDS > FB BEGINS
LIFELOG (DARPA) TEAM TRANSFER > FB
WHAT (DARPA) TEAM MEMBERS PAST/PRESENT WORK FOR FB?
WHAT DIVISIONS?
LOCATE (3) PUBLIC.
(9) TOTAL (6_NON PUB).
BUILDING 8 EXPOSED (HERE) WHEN?
[4-11-18]
*THINK SCRAMBLE [OFFLINE SCRUB] POST XBOX/PS CHAT LOGS DROP*
[MS SHUTDOWN IMMEDIATELY POST DROP]
BUILDING 8 NEWS RELEASE "RESTRUCTURING BUILDING 8" RELEASE?
[12-14-18] > RIP
https://techcrunch.com/2018/12/14/facebook-restructures-building-8-separating-projects-into-reality-labs-and-portal-groups/
RIP = FALSE
REORG = TRUE
CHINA-CHINA-CHINA
CHINA-CHINA-CHINA
[OPEN ACCESS - PAY FOR PLAY]
LAWS WHICH PREVENT C_A OPERATIONS INSIDE HOMELAND?
BULK DATA COLLECTION_NSA_HOMELAND?
BULK DATA COLLECTION_C_A_HOMELAND?
HOW DOES THE C_A AVOID LAW TRIGGER RE: UMBRELLA_SPY_HOMELAND?
FACEBOOK [CHINA_BUILDING 8]
GOOGLE [CHINA_DRAGONFLY]
TWITTER [US_LEG_TRACK]
FACEBOOK TRACK USER GPS, VOICE & TEXT?
GOOGLE TRACK USER GPS, VOICE & TEXT?
TWITTER TRACK USER GPS?
[PHONE_PAD_MICROPHONE_ALGO_EMBED]
ALL FOR MARKETING PURPOSES AS PUBLICLY DISCLOSED?
WHO HAS ACCESS TO BULK TRACK DATA?
WHO HAS ACCESS TO BULK DATA?
IF NSA HAS ABILITY TO 'ABSORB' DATA STREAM UT IN-HOUSE TOOLS, DOES C_A HAVE ABILITY TO 'COLLECT' DATA STREAM FROM 'FUNDED''NETWORKED' OFFSHOOTS [BIG TECH]?
OFFSHOOTS NECESSARY TO AVOID C_A BREACH OF US DOMESTIC LAW?
AMAZON SERVER/CLOUD CONTRACT?
AMAZON_SERVER/CLOUD_ROUTE_DATA 1-99 DOMESTIC?
C_A TASKED W/ GATHERING AND ANALYZING INFO ON FOREIGN GOVS + INDIVS? SIGINT - COV
NSA TASKED W/ GATHERING AND ANALYZING INFO ON A GLOBAL SCALE (INCLUDING DOMESTIC)? SIGINT - COV
WHAT FORMER US PRESIDENT WAS C_A DIRECTOR?
http://www.thedrive.com/the-war-zone/25241/george-h-w-bush-saved-the-cia
THINK C_A [BRENNAN] AUTH SPY CAMPAIGN US SENATE UNDER HUSSEIN.
THINK C_A INSTALL CAMPAIGN US HOUSE & SENATE INFILTRATION.
[PART 1 OF 9]
Q
Display Options
Delta to next: 3 D_16:36:35 (seconds total: 318995) (35) (8)
Q!!mG7VJxZNCI 03/03/2019 01:17:43 ID: 84ae7e
8chan/qresearch: 5477272Q Clock [ Min: 31 | :25/:55 Mir: 19 | 180 Mir: 1 | :35/:05 Mir: 39 ]
Delta to Reply: 0 D_00:12:14 (seconds total: 734) (14) (5)
Epoch: 1551593129 (41) (5)
Anonymous 03/03/2019 01:05:29 ID:801c7c 8chan/qresearch: 5477001
>>5476889
Check #2657
YUUUGE
When will the public discover that Ted Cruz was also illegally SURV (pre_POTUS_R nomination)?
C_A 'illegal' SURV > members of Congress?
C_A 'illegal' SURV > members of the Press?
C_A 'illegal' SURV > SENATE INTEL COMM?
https://www.theguardian.com/us-news/2016/sep/10/cia-senate-investigation-constitutional-crisis-daniel-jones
https://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html
Who ordered the SURV?
What justification was provided to AUTH SURV of ELECTED OFFICIALS?
SURV fall under scope of FISA warrant or internal to Dept or outsourced to FVEY?
Reality check - friend or foe, we all spy on each other?
Should we be spying on ourselves?
Should we be tasking others to spy on ourselves in order to avoid U.S. law?
Was FVEY established designed by the INTEL COMM as a backchannel SURV apparatus to avoid domestic laws triggers and Congressional/Senate oversight?
What keylogs exist to monitor FVEY intel collection?
What ability do former GOV officials have re: ability to access C_LEVEL FVEY offshore data?
How did HRC gain access to highest CLAS SAPs (closed system access) and able to transfer to remote/home server?
(Q above should scare every single American)
How did CHINA locate primary C_A assets within CHINA [187]?
Money buys POWER.
No punishment [Brennan] by HUSSEIN ADMIN re: SURV of Senate etc?
…..
Check #2657
YUUUGE
When will the public discover that Ted Cruz was also illegally SURV (pre_POTUS_R nomination)?
C_A 'illegal' SURV > members of Congress?
C_A 'illegal' SURV > members of the Press?
C_A 'illegal' SURV > SENATE INTEL COMM?
https://www.theguardian.com/us-news/2016/sep/10/cia-senate-investigation-constitutional-crisis-daniel-jones
https://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html
Who ordered the SURV?
What justification was provided to AUTH SURV of ELECTED OFFICIALS?
SURV fall under scope of FISA warrant or internal to Dept or outsourced to FVEY?
Reality check - friend or foe, we all spy on each other?
Should we be spying on ourselves?
Should we be tasking others to spy on ourselves in order to avoid U.S. law?
Was FVEY established designed by the INTEL COMM as a backchannel SURV apparatus to avoid domestic laws triggers and Congressional/Senate oversight?
What keylogs exist to monitor FVEY intel collection?
What ability do former GOV officials have re: ability to access C_LEVEL FVEY offshore data?
How did HRC gain access to highest CLAS SAPs (closed system access) and able to transfer to remote/home server?
(Q above should scare every single American)
How did CHINA locate primary C_A assets within CHINA [187]?
Money buys POWER.
No punishment [Brennan] by HUSSEIN ADMIN re: SURV of Senate etc?
…..
>>5477001
Display Options
Delta to next: 12 D_04:54:58 (seconds total: 1054498) (31) (4)
Q!!mG7VJxZNCI 02/18/2019 20:22:45 ID: c8ae0b
8chan/qresearch: 5253402Q Clock [ Min: 18 | :25/:55 Mir: 32 | 180 Mir: 48 | :35/:05 Mir: 52 ]
Pick a Network – Any Network.
Search ‘Qanon’
https://www.nbcnews.com/pages/search/?q=qanon
https://abcnews.go.com/search?searchtext=qanon
https://www.washingtonpost.com/newssearch/?datefilter=All%20Since%202005&query=qanon&sort=Relevance&utm_term=.d3e179a0682e
https://www.nytimes.com/search?query=qanon
https://www.cnn.com/search/?q=qanon
http://www.msnbc.com/search/qanon
https://www.newsweek.com/search/site/qanon
http://fortune.com/search/?q=qanon
https://www.wired.com/search/?q=qanon&page=1&sort=score
https://www.theguardian.com/us (search: Qanon)
https://www.npr.org/search?query=qanon&page=1
https://www.vox.com/search?q=qanon
https://www.gq.com/search?q=qanon
https://www.pbs.org/search/?q=qanon
https://www.theverge.com/search?q=qanon
https://observer.com/?s=qanon
https://www.aljazeera.com/Search/?q=qanon
https://www.foxnews.com/search-results/search?q=qanon
https://www.breitbart.com/search/?s=qanon#gsc.tab=0&gsc.q=qanon&gsc.page=1
https://psmag.com/search?query=qanon
https://www.newyorker.com/search/q/qanon
https://www.latimes.com/search/?q=qanon
https://www.seattletimes.com/search/?query=qanon&sortby=mostrecent&page=1&perpage=20
https://www.esquire.com/search/?q=qanon
https://www.thesun.co.uk/?s=qanon
https://www.bbc.co.uk/search?q=qanon
https://www.jpost.com/Arab-Israeli-Conflict/Muslim-woman-fights-for-Israel-despite-death-threats-watch-581066#/search;query=qanon
https://qz.com/search/qanon/
http://nymag.com/search.html?q=qanon
https://www.politico.com/search?q=qanon
https://thehill.com/search/site/qanon
https://search.huffingtonpost.com/search?utf8=✓&p=qanon&fr=huffpost
http://time.com/search/?q=qanon
https://www.vice.com/en_us/search?q=qanon
https://www.salon.com/search/qanon
https://www.dailydot.com/?s=qanon
https://www.miaminewtimes.com/search?keyword=qanon
https://www.rollingstone.com/results/#?q=qanon
https://motherboard.vice.com/en_us/search?q=qanon
https://www.snopes.com/?s=qanon
https://www.buzzfeed.com/search?q=qanon
https://www.mediamatters.org/search/index?qstring=qanon
http://thefederalist.com/?s=qanon
Reconcile.
Q
Search ‘Qanon’
https://www.nbcnews.com/pages/search/?q=qanon
https://abcnews.go.com/search?searchtext=qanon
https://www.washingtonpost.com/newssearch/?datefilter=All%20Since%202005&query=qanon&sort=Relevance&utm_term=.d3e179a0682e
https://www.nytimes.com/search?query=qanon
https://www.cnn.com/search/?q=qanon
http://www.msnbc.com/search/qanon
https://www.newsweek.com/search/site/qanon
http://fortune.com/search/?q=qanon
https://www.wired.com/search/?q=qanon&page=1&sort=score
https://www.theguardian.com/us (search: Qanon)
https://www.npr.org/search?query=qanon&page=1
https://www.vox.com/search?q=qanon
https://www.gq.com/search?q=qanon
https://www.pbs.org/search/?q=qanon
https://www.theverge.com/search?q=qanon
https://observer.com/?s=qanon
https://www.aljazeera.com/Search/?q=qanon
https://www.foxnews.com/search-results/search?q=qanon
https://www.breitbart.com/search/?s=qanon#gsc.tab=0&gsc.q=qanon&gsc.page=1
https://psmag.com/search?query=qanon
https://www.newyorker.com/search/q/qanon
https://www.latimes.com/search/?q=qanon
https://www.seattletimes.com/search/?query=qanon&sortby=mostrecent&page=1&perpage=20
https://www.esquire.com/search/?q=qanon
https://www.thesun.co.uk/?s=qanon
https://www.bbc.co.uk/search?q=qanon
https://www.jpost.com/Arab-Israeli-Conflict/Muslim-woman-fights-for-Israel-despite-death-threats-watch-581066#/search;query=qanon
https://qz.com/search/qanon/
http://nymag.com/search.html?q=qanon
https://www.politico.com/search?q=qanon
https://thehill.com/search/site/qanon
https://search.huffingtonpost.com/search?utf8=✓&p=qanon&fr=huffpost
http://time.com/search/?q=qanon
https://www.vice.com/en_us/search?q=qanon
https://www.salon.com/search/qanon
https://www.dailydot.com/?s=qanon
https://www.miaminewtimes.com/search?keyword=qanon
https://www.rollingstone.com/results/#?q=qanon
https://motherboard.vice.com/en_us/search?q=qanon
https://www.snopes.com/?s=qanon
https://www.buzzfeed.com/search?q=qanon
https://www.mediamatters.org/search/index?qstring=qanon
http://thefederalist.com/?s=qanon
Reconcile.
Q
Display Options
Delta to next: 7 D_07:31:59 (seconds total: 631919) (29) (2)
Q!!mG7VJxZNCI 02/11/2019 12:50:46 ID: 82893e
8chan/qresearch: 5123215Q Clock [ Min: 11 | :25/:55 Mir: 39 | 180 Mir: 41 | :35/:05 Mir: 59 ]
Delta to Reply: 0 D_00:00:24 (seconds total: 24) (6) (6)
Epoch: 1549907422 (43) (7)
Q !!mG7VJxZNCI02/11/2019 12:50:22 ID:82893e 8chan/qresearch: 5123210
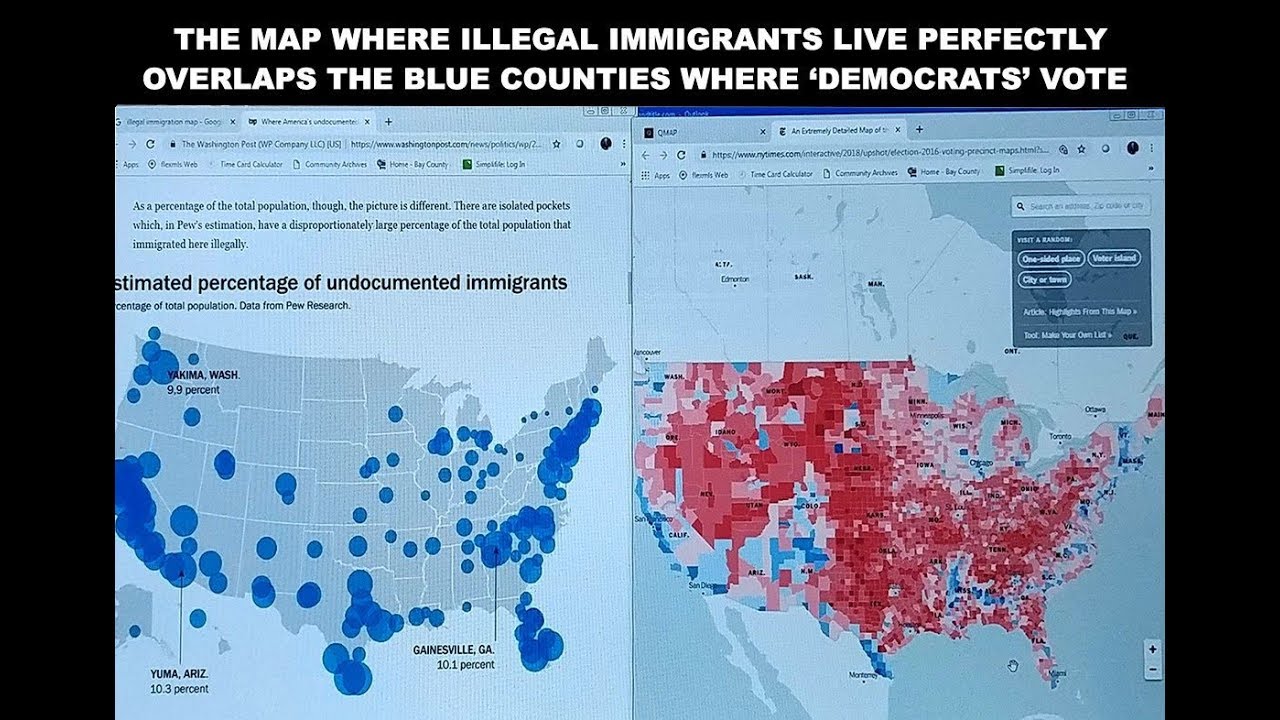
Image Name: VoterFraud.jpg
Filename: c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
EXIF DATA
name : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1280
geometry.height : 720
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 921600
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1280
pageGeometry.height : 720
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 89
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : b7bde8a460d9effd71033ebedc51f20f4a1157f90d6a3bdd447a4c1aa8bf4ad2
tainted :
filesize : 198903
numberPixels : 921600
filename : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
name : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1280
geometry.height : 720
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 921600
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1280
pageGeometry.height : 720
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 89
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : b7bde8a460d9effd71033ebedc51f20f4a1157f90d6a3bdd447a4c1aa8bf4ad2
tainted :
filesize : 198903
numberPixels : 921600
filename : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
https://www.justice.gov/opa/pr/acting-attorney-general-and-secretary-homeland-security-submit-joint-report-impact-foreign
[Only when the election harms the D party will they claim foreign interference]
Keyword: 'Foreign'
What about Domestic interference?
>Non-Cit votes by county
>Non-Cit promo by county
>Non-Cit org by county
>Targeted districts breakdown by 'Non-Cit' data acc
>Voter irregularities [internal]
>(-2) Laws enacted in battleground areas as test for 2020 (voter roll screening/review of non_votes (D) > ballot pop > track for sign > submit late for count) - vote swing figures + rule of law (new standard of no show vote SC 2019 scope case?)
Why do D's push for NO VOTER ID in U.S. elections?
Why do D's push for OPEN BORDERS?
Find the connection.
Sometimes a MAP helps.
What SC decision (6-3) ruled VOTER ID did NOT suppress votes or deter minorities?
https://www.reuters.com/article/us-usa-politics-court/supreme-court-upholds-photo-id-voting-law-idUSWAT00940020080428
What (FALSE) 'narrative' is pushed by D's re: VOTER ID LAW?
Racist?
Voter suppression of minority vote?
When is an ID required?
Should an ID not be required at all (for any reason) given the argument made by D's?
Does the argument 'A NATIONAL VOTER ID LAW would suppress the minority vote' suggest minorities are incapable of obtaining an ID?
When is an ID required?
Which minorities are they referring to?
(illegal immigrants?)
Logical thinking.
If there is a previous SC decision on the matter (pre-POTUS Justice conf), would a NATIONAL VOTER ID LAW MANDATE using the SC ruling of 2008 (+ common sense logic/arguments) as the LEGAL FOUNDATION, have merit?
Is every other country that has a VOTER ID LAW considered racist?
https://www.newsobserver.com/news/politics-government/state-politics/article92593512.html
Will the DOJ support the push instead of file legal challenges as [LL] did in the past?
If the SC ruled in 2008 that VOTER ID laws do not impact/harm or prevent 'minorities' from voting, how could the U.S. 4th Circuit Court rule opposite?
Is the 4th Circuit Court considered LEFT/Liberal?
https://www.newsobserver.com/news/politics-government/article215247000.html
Why do D's want POWER at all costs?
One example above.
Logical thinking.
#FactsMatter
You are the news now.
Q
[Only when the election harms the D party will they claim foreign interference]
Keyword: 'Foreign'
What about Domestic interference?
>Non-Cit votes by county
>Non-Cit promo by county
>Non-Cit org by county
>Targeted districts breakdown by 'Non-Cit' data acc
>Voter irregularities [internal]
>(-2) Laws enacted in battleground areas as test for 2020 (voter roll screening/review of non_votes (D) > ballot pop > track for sign > submit late for count) - vote swing figures + rule of law (new standard of no show vote SC 2019 scope case?)
Why do D's push for NO VOTER ID in U.S. elections?
Why do D's push for OPEN BORDERS?
Find the connection.
Sometimes a MAP helps.
What SC decision (6-3) ruled VOTER ID did NOT suppress votes or deter minorities?
https://www.reuters.com/article/us-usa-politics-court/supreme-court-upholds-photo-id-voting-law-idUSWAT00940020080428
What (FALSE) 'narrative' is pushed by D's re: VOTER ID LAW?
Racist?
Voter suppression of minority vote?
When is an ID required?
Should an ID not be required at all (for any reason) given the argument made by D's?
Does the argument 'A NATIONAL VOTER ID LAW would suppress the minority vote' suggest minorities are incapable of obtaining an ID?
When is an ID required?
Which minorities are they referring to?
(illegal immigrants?)
Logical thinking.
If there is a previous SC decision on the matter (pre-POTUS Justice conf), would a NATIONAL VOTER ID LAW MANDATE using the SC ruling of 2008 (+ common sense logic/arguments) as the LEGAL FOUNDATION, have merit?
Is every other country that has a VOTER ID LAW considered racist?
https://www.newsobserver.com/news/politics-government/state-politics/article92593512.html
Will the DOJ support the push instead of file legal challenges as [LL] did in the past?
If the SC ruled in 2008 that VOTER ID laws do not impact/harm or prevent 'minorities' from voting, how could the U.S. 4th Circuit Court rule opposite?
Is the 4th Circuit Court considered LEFT/Liberal?
https://www.newsobserver.com/news/politics-government/article215247000.html
Why do D's want POWER at all costs?
One example above.
Logical thinking.
#FactsMatter
You are the news now.
Q

Image Name: Drr-_hrXcAEV77j.jpg
Filename: 4458313fc2d1ca66feb5eaf6fe6f885669cef5c48cef59d7a0b05bbf8a1ca903.jpg
EXIF DATA
name : 4458313fc2d1ca66feb5eaf6fe6f885669cef5c48cef59d7a0b05bbf8a1ca903.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 500
geometry.height : 460
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 230000
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 500
pageGeometry.height : 460
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : a0ab7d3b4e45cea20e981800969469163b73b089e81aaaa30a20dd2cf67514e2
tainted :
filesize : 67566
numberPixels : 230000
filename : 4458313fc2d1ca66feb5eaf6fe6f885669cef5c48cef59d7a0b05bbf8a1ca903.jpg
name : 4458313fc2d1ca66feb5eaf6fe6f885669cef5c48cef59d7a0b05bbf8a1ca903.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 500
geometry.height : 460
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 230000
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 500
pageGeometry.height : 460
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : a0ab7d3b4e45cea20e981800969469163b73b089e81aaaa30a20dd2cf67514e2
tainted :
filesize : 67566
numberPixels : 230000
filename : 4458313fc2d1ca66feb5eaf6fe6f885669cef5c48cef59d7a0b05bbf8a1ca903.jpg
Image Search Tags:
>>5123210
Display Options
Delta to next: 0 D_00:00:24 (seconds total: 24) (6) (6)
Q!!mG7VJxZNCI 02/11/2019 12:50:22 ID: 82893e
8chan/qresearch: 5123210Q Clock [ Min: 11 | :25/:55 Mir: 39 | 180 Mir: 41 | :35/:05 Mir: 59 ]
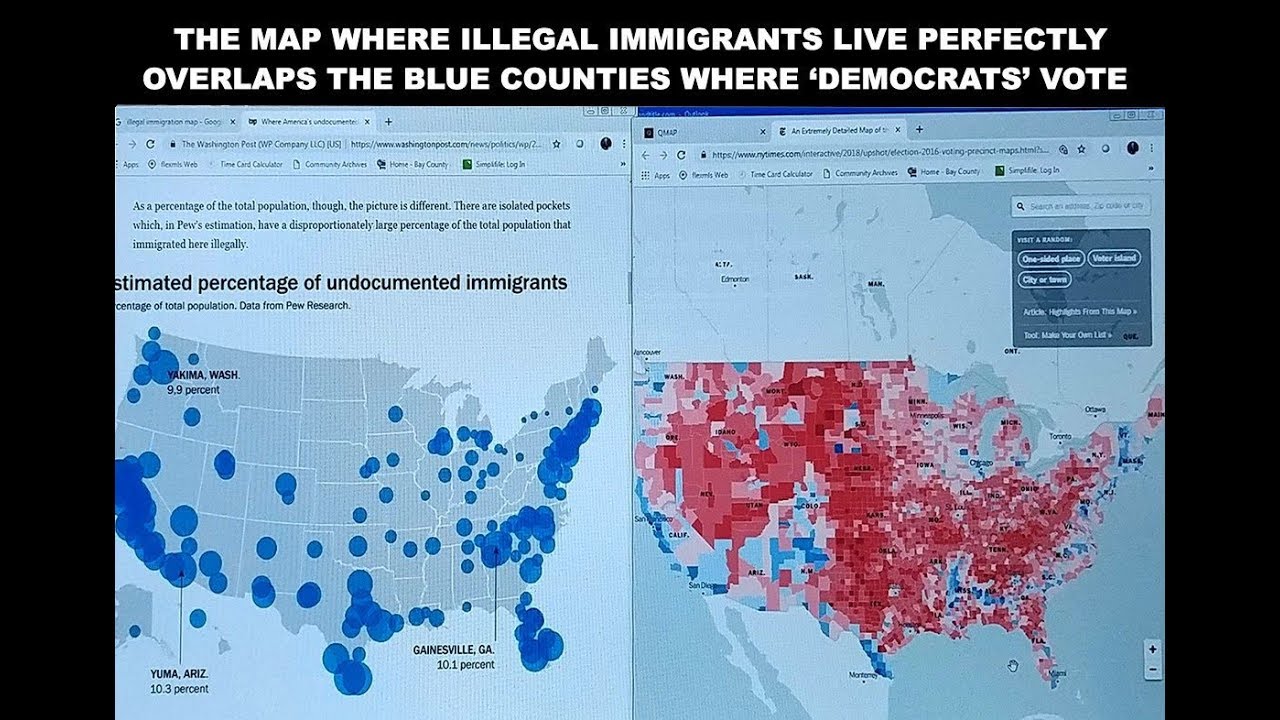
Image Name: VoterFraud.jpg
Filename: c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
EXIF DATA
name : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1280
geometry.height : 720
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 921600
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1280
pageGeometry.height : 720
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 89
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : b7bde8a460d9effd71033ebedc51f20f4a1157f90d6a3bdd447a4c1aa8bf4ad2
tainted :
filesize : 198903
numberPixels : 921600
filename : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
name : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1280
geometry.height : 720
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 921600
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 1280
pageGeometry.height : 720
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 89
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : b7bde8a460d9effd71033ebedc51f20f4a1157f90d6a3bdd447a4c1aa8bf4ad2
tainted :
filesize : 198903
numberPixels : 921600
filename : c1bf60fe3efac2a7ccd4447f0e3f99cae10f3758af66fdb55e65adf7e88e2b31.jpg
Image Search Tags:
https://www.justice.gov/opa/pr/acting-attorney-general-and-secretary-homeland-security-submit-joint-report-impact-foreign
[Only when the election harms the D party will they claim foreign interference]
Keyword: 'Foreign'
What about Domestic interference?
>Non-Cit votes by county
>Non-Cit promo by county
>Non-Cit org by county
>Targeted districts breakdown by 'Non-Cit' data acc
>Voter irregularities [internal]
>(-2) Laws enacted in battleground areas as test for 2020 (voter roll screening/review of non_votes (D) > ballot pop > track for sign > submit late for count) - vote swing figures + rule of law (new standard of no show vote SC 2019 scope case?)
Why do D's push for NO VOTER ID in U.S. elections?
Why do D's push for OPEN BORDERS?
Find the connection.
Sometimes a MAP helps.
What SC decision (6-3) ruled VOTER ID did NOT suppress votes or deter minorities?
https://www.reuters.com/article/us-usa-politics-court/supreme-court-upholds-photo-id-voting-law-idUSWAT00940020080428
What (FALSE) 'narrative' is pushed by D's re: VOTER ID LAW?
Racist?
Voter suppression of minority vote?
When is an ID required?
Should an ID not be required at all (for any reason) given the argument made by D's?
Does the argument 'A NATIONAL VOTER ID LAW would suppress the minority vote' suggest minorities are incapable of obtaining an ID?
When is an ID required?
Which minorities are they referring to?
(illegal immigrants?)
Logical thinking.
If there is a previous SC decision on the matter (pre-POTUS Justice conf), would a NATIONAL VOTER ID LAW MANDATE using the SC ruling of 2008 (+ common sense logic/arguments) as the LEGAL FOUNDATION, have merit?
Is every other country that has a VOTER ID LAW considered racist?
https://www.newsobserver.com/news/politics-government/state-politics/article92593512.html
Will the DOJ support the push instead of file legal challenges as [LL] did in the past?
If the SC ruled in 2008 that VOTER ID laws do not impact/harm or prevent 'minorities' from voting, how could the U.S. 4th Circuit Court rule opposite?
Is the 4th Circuit Court considered LEFT/Liberal?
https://www.newsobserver.com/news/politics-government/article215247000.html
Why do D's want POWER at all costs?
One example above.
Logical thinking.
#FactsMatter
You are the news now.
Q
[Only when the election harms the D party will they claim foreign interference]
Keyword: 'Foreign'
What about Domestic interference?
>Non-Cit votes by county
>Non-Cit promo by county
>Non-Cit org by county
>Targeted districts breakdown by 'Non-Cit' data acc
>Voter irregularities [internal]
>(-2) Laws enacted in battleground areas as test for 2020 (voter roll screening/review of non_votes (D) > ballot pop > track for sign > submit late for count) - vote swing figures + rule of law (new standard of no show vote SC 2019 scope case?)
Why do D's push for NO VOTER ID in U.S. elections?
Why do D's push for OPEN BORDERS?
Find the connection.
Sometimes a MAP helps.
What SC decision (6-3) ruled VOTER ID did NOT suppress votes or deter minorities?
https://www.reuters.com/article/us-usa-politics-court/supreme-court-upholds-photo-id-voting-law-idUSWAT00940020080428
What (FALSE) 'narrative' is pushed by D's re: VOTER ID LAW?
Racist?
Voter suppression of minority vote?
When is an ID required?
Should an ID not be required at all (for any reason) given the argument made by D's?
Does the argument 'A NATIONAL VOTER ID LAW would suppress the minority vote' suggest minorities are incapable of obtaining an ID?
When is an ID required?
Which minorities are they referring to?
(illegal immigrants?)
Logical thinking.
If there is a previous SC decision on the matter (pre-POTUS Justice conf), would a NATIONAL VOTER ID LAW MANDATE using the SC ruling of 2008 (+ common sense logic/arguments) as the LEGAL FOUNDATION, have merit?
Is every other country that has a VOTER ID LAW considered racist?
https://www.newsobserver.com/news/politics-government/state-politics/article92593512.html
Will the DOJ support the push instead of file legal challenges as [LL] did in the past?
If the SC ruled in 2008 that VOTER ID laws do not impact/harm or prevent 'minorities' from voting, how could the U.S. 4th Circuit Court rule opposite?
Is the 4th Circuit Court considered LEFT/Liberal?
https://www.newsobserver.com/news/politics-government/article215247000.html
Why do D's want POWER at all costs?
One example above.
Logical thinking.
#FactsMatter
You are the news now.
Q
Display Options
Delta to next: 35 D_21:41:13 (seconds total: 3102073) (16) (7)
Q!!mG7VJxZNCI 01/06/2019 15:09:09 ID: 1bfec6
8chan/qresearch: 4630322Q Clock [ Min: 35 | :25/:55 Mir: 15 | 180 Mir: 5 | :35/:05 Mir: 35 ]
When will the public discover that Ted Cruz was also illegally SURV (pre_POTUS_R nomination)?
C_A 'illegal' SURV > members of Congress?
C_A 'illegal' SURV > members of the Press?
C_A 'illegal' SURV > SENATE INTEL COMM?
https://www.theguardian.com/us-news/2016/sep/10/cia-senate-investigation-constitutional-crisis-daniel-jones
https://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html
Who ordered the SURV?
What justification was provided to AUTH SURV of ELECTED OFFICIALS?
SURV fall under scope of FISA warrant or internal to Dept or outsourced to FVEY?
Reality check - friend or foe, we all spy on each other?
Should we be spying on ourselves?
Should we be tasking others to spy on ourselves in order to avoid U.S. law?
Was FVEY established & designed by the INTEL COMM as a backchannel SURV apparatus to avoid domestic laws triggers and Congressional/Senate oversight?
What keylogs exist to monitor FVEY intel collection?
What ability do former GOV officials have re: ability to access C_LEVEL FVEY offshore data?
How did HRC gain access to highest CLAS SAPs (closed system access) and able to transfer to remote/home server?
(Q above should scare every single American)
How did CHINA locate primary C_A assets within CHINA [187]?
Money buys POWER.
No punishment [Brennan] by HUSSEIN ADMIN re: SURV of Senate etc?
Logical thinking, why?
https://www.mcclatchydc.com/news/nation-world/national/national-security/article24770296.html
Justice Dept declines to pursue?
Fake News media limits exposure to public?
When did @Snowden breach NSA & PUBLICLY RELEASE (CRIPPLE) INTEL GATHERING ABILITY (NSA)?
NSA targeted?
Where did @Snowden work prior to NSA contractor ACCEPT?
What SENIOR LEVEL GOV/C_A OFFICIAL rec @Snowden for NSA contractor OFF/TAR position?
Post public release of CLAS NSA PRO > U1?
Where is @Snowden today?
What country was involved in U1?
If real target country was VENEZUELA or ECUADOR - why didn't @Snowden take a direct flight from Hong Kong to those locations?
How many direct flights run daily from HK to V&E?
If @Snowden was C_A/NSA would he not understand (simple logic) going public PRIOR TO END DESTINATION SAFETY would 'LIMIT' ACTIVE PASSPORT TRAVEL ABILITY due to block_DEREG?
WHY WOULDN'T @Snowden PUBLICLY RELEASE INFO AFTER HE ALREADY WAS SAFELY AT FINAL DESTINATION?
Why then would @Snowden route through RUSSIA?
Was RUSSIA final destination?
Was RUSSIA true destination?
Could @Snowden be seen releasing CLAS programs/intel FROM INSIDE OF RUSSIA?
What role did BRENNAN PLAY in the @Snowden leaks re: NSA?
What was BRENNAN's background re: SAUDI ARABIA?
Does the C_A hold blackmail on political leaders?
Does the C_A protect those who protect them?
Why are ex C_A contractors running for office?
How many ex C_A contractors are currently in office?
Hello, [AS].
Once an agent, always an agent.
Q
C_A 'illegal' SURV > members of Congress?
C_A 'illegal' SURV > members of the Press?
C_A 'illegal' SURV > SENATE INTEL COMM?
https://www.theguardian.com/us-news/2016/sep/10/cia-senate-investigation-constitutional-crisis-daniel-jones
https://www.nytimes.com/2014/08/01/world/senate-intelligence-commitee-cia-interrogation-report.html
Who ordered the SURV?
What justification was provided to AUTH SURV of ELECTED OFFICIALS?
SURV fall under scope of FISA warrant or internal to Dept or outsourced to FVEY?
Reality check - friend or foe, we all spy on each other?
Should we be spying on ourselves?
Should we be tasking others to spy on ourselves in order to avoid U.S. law?
Was FVEY established & designed by the INTEL COMM as a backchannel SURV apparatus to avoid domestic laws triggers and Congressional/Senate oversight?
What keylogs exist to monitor FVEY intel collection?
What ability do former GOV officials have re: ability to access C_LEVEL FVEY offshore data?
How did HRC gain access to highest CLAS SAPs (closed system access) and able to transfer to remote/home server?
(Q above should scare every single American)
How did CHINA locate primary C_A assets within CHINA [187]?
Money buys POWER.
No punishment [Brennan] by HUSSEIN ADMIN re: SURV of Senate etc?
Logical thinking, why?
https://www.mcclatchydc.com/news/nation-world/national/national-security/article24770296.html
Justice Dept declines to pursue?
Fake News media limits exposure to public?
When did @Snowden breach NSA & PUBLICLY RELEASE (CRIPPLE) INTEL GATHERING ABILITY (NSA)?
NSA targeted?
Where did @Snowden work prior to NSA contractor ACCEPT?
What SENIOR LEVEL GOV/C_A OFFICIAL rec @Snowden for NSA contractor OFF/TAR position?
Post public release of CLAS NSA PRO > U1?
Where is @Snowden today?
What country was involved in U1?
If real target country was VENEZUELA or ECUADOR - why didn't @Snowden take a direct flight from Hong Kong to those locations?
How many direct flights run daily from HK to V&E?
If @Snowden was C_A/NSA would he not understand (simple logic) going public PRIOR TO END DESTINATION SAFETY would 'LIMIT' ACTIVE PASSPORT TRAVEL ABILITY due to block_DEREG?
WHY WOULDN'T @Snowden PUBLICLY RELEASE INFO AFTER HE ALREADY WAS SAFELY AT FINAL DESTINATION?
Why then would @Snowden route through RUSSIA?
Was RUSSIA final destination?
Was RUSSIA true destination?
Could @Snowden be seen releasing CLAS programs/intel FROM INSIDE OF RUSSIA?
What role did BRENNAN PLAY in the @Snowden leaks re: NSA?
What was BRENNAN's background re: SAUDI ARABIA?
Does the C_A hold blackmail on political leaders?
Does the C_A protect those who protect them?
Why are ex C_A contractors running for office?
How many ex C_A contractors are currently in office?
Hello, [AS].
Once an agent, always an agent.
Q
Display Options
Delta to next: 24 D_20:16:30 (seconds total: 2146590) (27) (9)
Q!!mG7VJxZNCI 12/12/2018 18:52:39 ID: 089200
8chan/qresearch: 4280615Q Clock [ Min: 10 | :25/:55 Mir: 40 | 180 Mir: 40 | :35/:05 Mir: 0 ]
Delta to Reply: 0 D_00:02:26 (seconds total: 146) (11) (2)
Epoch: 1544658613 (43) (7)
Anonymous 12/12/2018 18:50:13 ID:e396ee 8chan/qresearch: 4280575
>>4280189
Is this a stress test?
Is this a stress test?
>>4280575
Yes.
Added server(s)/bandwidth improved performance.
Q
Yes.
Added server(s)/bandwidth improved performance.
Q
Display Options
Delta to next: 7 D_19:09:44 (seconds total: 673784) (35) (8)
Q!!mG7VJxZNCI 12/04/2018 23:42:55 ID: 44a34b
8chan/qresearch: 4158232Q Clock [ Min: 2 | :25/:55 Mir: 48 | 180 Mir: 32 | :35/:05 Mir: 8 ]
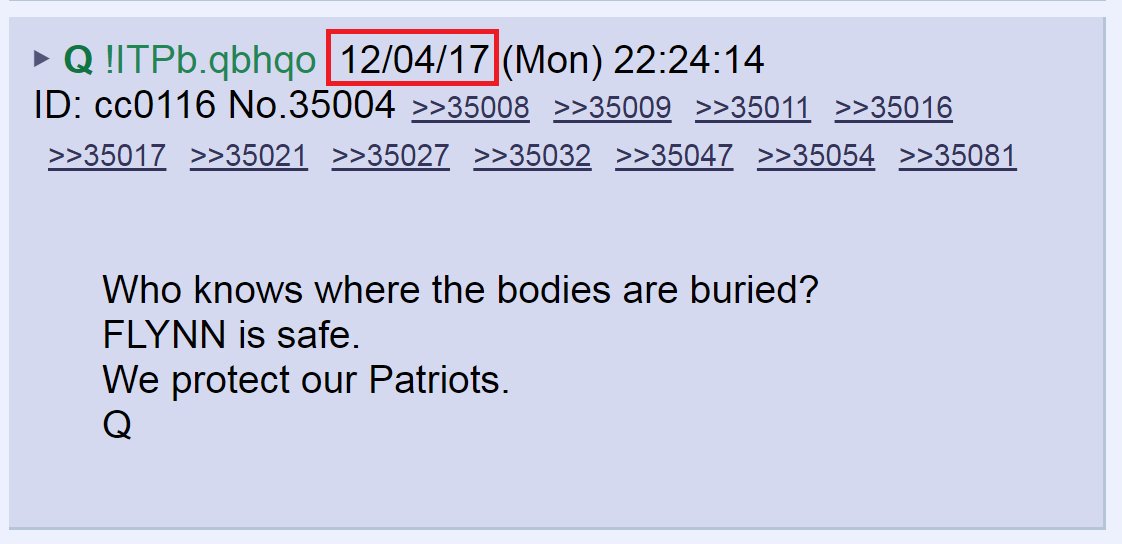
Image Name: Dc43CR5WAAAy400.jpg-large.jpg
Filename: 74b0b7b8188edc3c4ffb912e0a5782eec5bdcdfb2da62a4033732c2e91d139df.jpg
EXIF DATA
name : 74b0b7b8188edc3c4ffb912e0a5782eec5bdcdfb2da62a4033732c2e91d139df.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1122
geometry.height : 544
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 610368
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1122
pageGeometry.height : 544
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 2f886fdb97e0cda443f617ba3ff5c188c328bf06d00d88628e85eaa1da9b2777
tainted :
filesize : 66481
numberPixels : 610368
filename : 74b0b7b8188edc3c4ffb912e0a5782eec5bdcdfb2da62a4033732c2e91d139df.jpg
name : 74b0b7b8188edc3c4ffb912e0a5782eec5bdcdfb2da62a4033732c2e91d139df.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1122
geometry.height : 544
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 610368
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1122
pageGeometry.height : 544
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 2f886fdb97e0cda443f617ba3ff5c188c328bf06d00d88628e85eaa1da9b2777
tainted :
filesize : 66481
numberPixels : 610368
filename : 74b0b7b8188edc3c4ffb912e0a5782eec5bdcdfb2da62a4033732c2e91d139df.jpg
Image Search Tags:
https://twitter.com/Tom_Winter/status/1070140182907756544
[Dec 4, 2018]
https://twitter.com/Tom_Winter/status/1070138096916799488
"NBC News: There appears, although the redacted documents do not make it completely clear, that there is a [[[+++separate criminal investigation going on outside of Special Counsel Robert Mueller's purview+++]]] for which Flynn has been providing significant assistance."
Markers are important.
[Dec 4, 2017] > [Dec 4, 2018]
Think No Name.
Did Mueller have a choice in making the recommendation?
Who does Mueller 'now' report to?
Does WHITAKER also oversee HUBER + OIG?
What case(s) is HUBER + OIG + team of 470 currently working on?
Who has the server(s)?
Who has access to NSA UT Term1-12?
Does FISA grant access to NSA umbrella collection?
You are witnessing something [firsthand] that many cannot possibly comprehend or accept as reality [Sci-Fi or precision M_planning?]
Coincidences > > > reveal w/o violating NAT SEC
Coincidences > > > mathematically impossible to be 'FALSE'
Coincidences > > > bypass 'installed' restrictions to prevent future legal attachments
Comms understood? 5:5?
SENATE WAS THE TARGET.
Q
[Dec 4, 2018]
https://twitter.com/Tom_Winter/status/1070138096916799488
"NBC News: There appears, although the redacted documents do not make it completely clear, that there is a [[[+++separate criminal investigation going on outside of Special Counsel Robert Mueller's purview+++]]] for which Flynn has been providing significant assistance."
Markers are important.
[Dec 4, 2017] > [Dec 4, 2018]
Think No Name.
Did Mueller have a choice in making the recommendation?
Who does Mueller 'now' report to?
Does WHITAKER also oversee HUBER + OIG?
What case(s) is HUBER + OIG + team of 470 currently working on?
Who has the server(s)?
Who has access to NSA UT Term1-12?
Does FISA grant access to NSA umbrella collection?
You are witnessing something [firsthand] that many cannot possibly comprehend or accept as reality [Sci-Fi or precision M_planning?]
Coincidences > > > reveal w/o violating NAT SEC
Coincidences > > > mathematically impossible to be 'FALSE'
Coincidences > > > bypass 'installed' restrictions to prevent future legal attachments
Comms understood? 5:5?
SENATE WAS THE TARGET.
Q
Display Options
Delta to next: 61 D_07:20:02 (seconds total: 5296802) (32) (5)
Q!!mG7VJxZNCI 10/04/2018 17:22:53 ID:
8chan/patriotsfight: 334Q Clock [ Min: 1 | :25/:55 Mir: 49 | 180 Mir: 31 | :35/:05 Mir: 9 ]
Delta to Reply: 0 D_00:08:14 (seconds total: 494) (17) (8)
Epoch: 1538687679 (60) (6)
Q !!mG7VJxZNCI10/04/2018 17:14:39 ID: 8chan/patriotsfight: 333
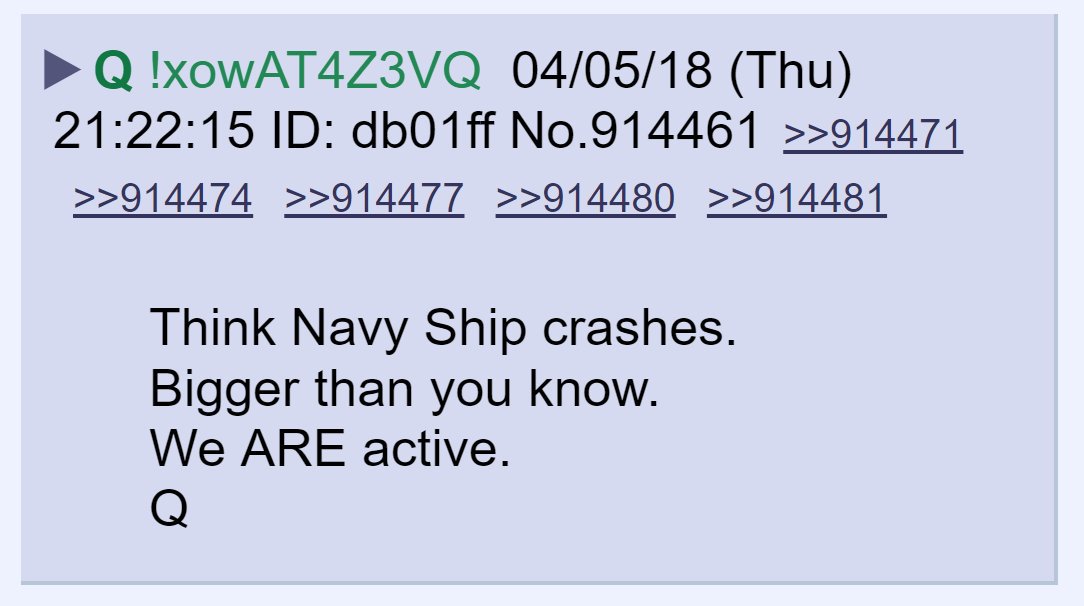
Image Name: DaHEgSOVwAEG-8h.jpg
Filename: 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
EXIF DATA
name : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1084
geometry.height : 606
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 656904
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1084
pageGeometry.height : 606
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 484bdd89d5da80125a9a92d8b84cb08be9a32017d9be55752e1a3bfd9e50c9de
tainted :
filesize : 66878
numberPixels : 656904
filename : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
name : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1084
geometry.height : 606
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 656904
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1084
pageGeometry.height : 606
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 484bdd89d5da80125a9a92d8b84cb08be9a32017d9be55752e1a3bfd9e50c9de
tainted :
filesize : 66878
numberPixels : 656904
filename : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
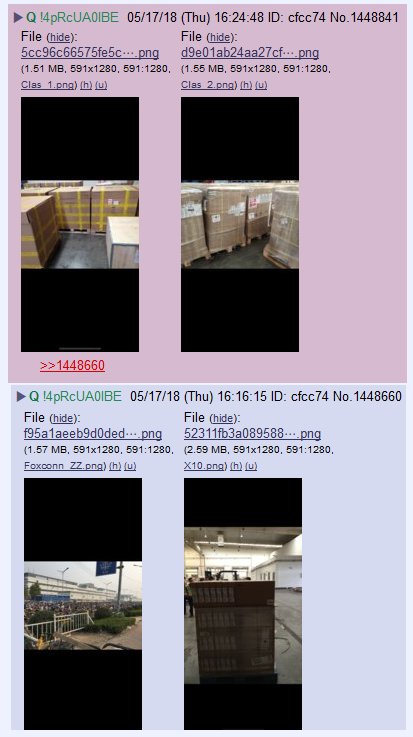
Image Name: DdcamI6WAAEyROC.jpg
Filename: 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
EXIF DATA
name : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 413
geometry.height : 737
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 304381
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 413
pageGeometry.height : 737
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : af011dd9a9143c0c70f65a3e3fe117db90d608ca1547f70542b7206624e25801
tainted :
filesize : 48809
numberPixels : 304381
filename : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
name : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 413
geometry.height : 737
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 304381
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 413
pageGeometry.height : 737
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : af011dd9a9143c0c70f65a3e3fe117db90d608ca1547f70542b7206624e25801
tainted :
filesize : 48809
numberPixels : 304381
filename : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
Image Name: DcPsu1PV0AEtzNc.jpg
Filename: 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
EXIF DATA
name : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 517
geometry.height : 1188
geometry.x : 0
geometry.y : 0
resolution.x : 72
resolution.y : 72
printSize.x : 7.18056
printSize.y : 16.5
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 614196
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 517
pageGeometry.height : 1188
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : e7247549260e2afe24095e8472b1b3504eb0fe01b0d7c18021f2e2a8dbae519e
tainted :
filesize : 114767
numberPixels : 614196
filename : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
name : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 517
geometry.height : 1188
geometry.x : 0
geometry.y : 0
resolution.x : 72
resolution.y : 72
printSize.x : 7.18056
printSize.y : 16.5
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 614196
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 517
pageGeometry.height : 1188
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : e7247549260e2afe24095e8472b1b3504eb0fe01b0d7c18021f2e2a8dbae519e
tainted :
filesize : 114767
numberPixels : 614196
filename : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
https://www.bloomberg.com/news/features/2018-10-04/the-big-hack-how-china-used-a-tiny-chip-to-infiltrate-america-s-top-companies
"Elemental’s servers could be found in Department of Defense data centers, the CIA’s drone operations, and the onboard networks of Navy warships."
"Multiple people familiar with the matter say investigators found that the chips had been inserted at factories run by manufacturing subcontractors in China."
"One official says investigators found that it eventually affected almost 30 companies, including a major bank, government contractors, and the world’s most valuable company, Apple Inc."
"One country in particular has an advantage executing this kind of attack: China, which by some estimates makes 75 percent of the world’s mobile phones and 90 percent of its PCs."
"But that’s just what U.S. investigators found: The chips had been inserted during the manufacturing process, two officials say, by operatives from a unit of the People’s Liberation Army. In Supermicro, China’s spies appear to have found a perfect conduit for what U.S. officials now describe as the most significant supply chain attack known to have been carried out against American companies."
The More You Know…
Q
"Elemental’s servers could be found in Department of Defense data centers, the CIA’s drone operations, and the onboard networks of Navy warships."
"Multiple people familiar with the matter say investigators found that the chips had been inserted at factories run by manufacturing subcontractors in China."
"One official says investigators found that it eventually affected almost 30 companies, including a major bank, government contractors, and the world’s most valuable company, Apple Inc."
"One country in particular has an advantage executing this kind of attack: China, which by some estimates makes 75 percent of the world’s mobile phones and 90 percent of its PCs."
"But that’s just what U.S. investigators found: The chips had been inserted during the manufacturing process, two officials say, by operatives from a unit of the People’s Liberation Army. In Supermicro, China’s spies appear to have found a perfect conduit for what U.S. officials now describe as the most significant supply chain attack known to have been carried out against American companies."
The More You Know…
Q
Image Name: DHQ27100.png
Filename: dac7f41e3fda74a7daee9a61b0df32e92cd7efa211b4d1d90180a3b68272b732.png
EXIF DATA
name : dac7f41e3fda74a7daee9a61b0df32e92cd7efa211b4d1d90180a3b68272b732.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 588
geometry.height : 274
geometry.x : 0
geometry.y : 0
resolution.x : 47.24
resolution.y : 47.24
printSize.x : 12.4471
printSize.y : 5.80017
units : PixelsPerCentimeter
type : TrueColorAlpha
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.alpha : 1
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 161112
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFFFF
borderColor : #DFDFDFFF
matteColor : #BDBDBDFF
transparentColor : #00000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 588
pageGeometry.height : 274
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 6
properties.png:IHDR.color_type : 6 (RGBA)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 588, 274
properties.png:pHYs : x_res=4724, y_res=4724, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : f341551119f1cce025f2784232f10d3efddfb8c2f2cd3fffd45b9c95f86c55ba
tainted :
filesize : 17391
numberPixels : 161112
filename : dac7f41e3fda74a7daee9a61b0df32e92cd7efa211b4d1d90180a3b68272b732.png
name : dac7f41e3fda74a7daee9a61b0df32e92cd7efa211b4d1d90180a3b68272b732.png
format : PNG
formatDescription : Portable Network Graphics
mimeType : image/png
class : DirectClass
geometry.width : 588
geometry.height : 274
geometry.x : 0
geometry.y : 0
resolution.x : 47.24
resolution.y : 47.24
printSize.x : 12.4471
printSize.y : 5.80017
units : PixelsPerCentimeter
type : TrueColorAlpha
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.alpha : 1
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 161112
renderingIntent : Perceptual
gamma : 0.45455
backgroundColor : #FFFFFFFF
borderColor : #DFDFDFFF
matteColor : #BDBDBDFF
transparentColor : #00000000
interlace : None
intensity : Undefined
compose : Over
pageGeometry.width : 588
pageGeometry.height : 274
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : Zip
orientation : Undefined
properties.png:cHRM : chunk was found (see Chromaticity, above)
properties.png:gAMA : gamma=0.45455 (See Gamma, above)
properties.png:IHDR.bit-depth-orig : 8
properties.png:IHDR.bit_depth : 8
properties.png:IHDR.color-type-orig : 6
properties.png:IHDR.color_type : 6 (RGBA)
properties.png:IHDR.interlace_method : 0 (Not interlaced)
properties.png:IHDR.width,height : 588, 274
properties.png:pHYs : x_res=4724, y_res=4724, units=1
properties.png:sRGB : intent=0 (Perceptual Intent)
properties.signature : f341551119f1cce025f2784232f10d3efddfb8c2f2cd3fffd45b9c95f86c55ba
tainted :
filesize : 17391
numberPixels : 161112
filename : dac7f41e3fda74a7daee9a61b0df32e92cd7efa211b4d1d90180a3b68272b732.png
Image Name: T_ah2810.jpg
Filename: a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
EXIF DATA
name : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1042
geometry.height : 786
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 819012
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1042
pageGeometry.height : 786
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : d303baed38d166427b6b9f75595fea78d776ccf23e0e4f306c4587f31e8560e3
profiles.icc :
tainted :
filesize : 74233
numberPixels : 819012
filename : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
name : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1042
geometry.height : 786
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 819012
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1042
pageGeometry.height : 786
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : d303baed38d166427b6b9f75595fea78d776ccf23e0e4f306c4587f31e8560e3
profiles.icc :
tainted :
filesize : 74233
numberPixels : 819012
filename : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
Image Search Tags:
>>333
Display Options
Delta to next: 0 D_00:08:14 (seconds total: 494) (17) (8)
Q!!mG7VJxZNCI 10/04/2018 17:14:39 ID:
8chan/patriotsfight: 333Q Clock [ Min: 1 | :25/:55 Mir: 49 | 180 Mir: 31 | :35/:05 Mir: 9 ]
Image Name: DaHEgSOVwAEG-8h.jpg
Filename: 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
EXIF DATA
name : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1084
geometry.height : 606
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 656904
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1084
pageGeometry.height : 606
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 484bdd89d5da80125a9a92d8b84cb08be9a32017d9be55752e1a3bfd9e50c9de
tainted :
filesize : 66878
numberPixels : 656904
filename : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
name : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1084
geometry.height : 606
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 656904
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1084
pageGeometry.height : 606
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 484bdd89d5da80125a9a92d8b84cb08be9a32017d9be55752e1a3bfd9e50c9de
tainted :
filesize : 66878
numberPixels : 656904
filename : 5911b6f3492538a7f6cd6f35ad5636601e756c3fc309cf352688bb036d0a8684.jpg
Image Name: DdcamI6WAAEyROC.jpg
Filename: 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
EXIF DATA
name : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 413
geometry.height : 737
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 304381
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 413
pageGeometry.height : 737
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : af011dd9a9143c0c70f65a3e3fe117db90d608ca1547f70542b7206624e25801
tainted :
filesize : 48809
numberPixels : 304381
filename : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
name : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 413
geometry.height : 737
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 304381
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 413
pageGeometry.height : 737
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : af011dd9a9143c0c70f65a3e3fe117db90d608ca1547f70542b7206624e25801
tainted :
filesize : 48809
numberPixels : 304381
filename : 257dde32fbe415d513760787bc66f99906943669c6e12bb3319fb87c46edb2af.jpg
Image Name: DcPsu1PV0AEtzNc.jpg
Filename: 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
EXIF DATA
name : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 517
geometry.height : 1188
geometry.x : 0
geometry.y : 0
resolution.x : 72
resolution.y : 72
printSize.x : 7.18056
printSize.y : 16.5
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 614196
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 517
pageGeometry.height : 1188
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : e7247549260e2afe24095e8472b1b3504eb0fe01b0d7c18021f2e2a8dbae519e
tainted :
filesize : 114767
numberPixels : 614196
filename : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
name : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 517
geometry.height : 1188
geometry.x : 0
geometry.y : 0
resolution.x : 72
resolution.y : 72
printSize.x : 7.18056
printSize.y : 16.5
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 614196
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 517
pageGeometry.height : 1188
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : e7247549260e2afe24095e8472b1b3504eb0fe01b0d7c18021f2e2a8dbae519e
tainted :
filesize : 114767
numberPixels : 614196
filename : 74fa367d9e27e6c3c838b851c9e6bf21c92edc05c74370165930144ef5febdd2.jpg
Image Search Tags:
https://www.bloomberg.com/news/features/2018-10-04/the-big-hack-how-china-used-a-tiny-chip-to-infiltrate-america-s-top-companies
"Elemental’s servers could be found in Department of Defense data centers, the CIA’s drone operations, and the onboard networks of Navy warships."
"Multiple people familiar with the matter say investigators found that the chips had been inserted at factories run by manufacturing subcontractors in China."
"One official says investigators found that it eventually affected almost 30 companies, including a major bank, government contractors, and the world’s most valuable company, Apple Inc."
"One country in particular has an advantage executing this kind of attack: China, which by some estimates makes 75 percent of the world’s mobile phones and 90 percent of its PCs."
"But that’s just what U.S. investigators found: The chips had been inserted during the manufacturing process, two officials say, by operatives from a unit of the People’s Liberation Army. In Supermicro, China’s spies appear to have found a perfect conduit for what U.S. officials now describe as the most significant supply chain attack known to have been carried out against American companies."
The More You Know…
Q
"Elemental’s servers could be found in Department of Defense data centers, the CIA’s drone operations, and the onboard networks of Navy warships."
"Multiple people familiar with the matter say investigators found that the chips had been inserted at factories run by manufacturing subcontractors in China."
"One official says investigators found that it eventually affected almost 30 companies, including a major bank, government contractors, and the world’s most valuable company, Apple Inc."
"One country in particular has an advantage executing this kind of attack: China, which by some estimates makes 75 percent of the world’s mobile phones and 90 percent of its PCs."
"But that’s just what U.S. investigators found: The chips had been inserted during the manufacturing process, two officials say, by operatives from a unit of the People’s Liberation Army. In Supermicro, China’s spies appear to have found a perfect conduit for what U.S. officials now describe as the most significant supply chain attack known to have been carried out against American companies."
The More You Know…
Q
Display Options
Delta to next: 35 D_02:37:44 (seconds total: 3033464) (23) (5)
Q!!mG7VJxZNCI 08/30/2018 14:36:55 ID: c32199
8chan/qresearch: 2801155Q Clock [ Min: 26 | :25/:55 Mir: 24 | 180 Mir: 56 | :35/:05 Mir: 44 ]
http://www.foxnews.com/politics/2018/08/30/gohmert-doubles-down-after-fbi-dismisses-claim-clinton-server-hack.html
Has POTUS made a statement (since being elected) that didn't end up being proven FACTUALLY TRUE?
Everything stated by POTUS will be made PUBLIC.
Follow the LEADER.
Focus Here:
"The ICIG declined to comment."
Q
Has POTUS made a statement (since being elected) that didn't end up being proven FACTUALLY TRUE?
Everything stated by POTUS will be made PUBLIC.
Follow the LEADER.
Focus Here:
"The ICIG declined to comment."
Q
Display Options
Delta to next: 0 D_22:48:29 (seconds total: 82109) (20) (2)
Q!!mG7VJxZNCI 08/29/2018 15:48:26 ID: 1c17fd
8chan/qresearch: 2786552Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Shall We Play A Game?
https://www.dni.gov/index.php/ctiic-who-we-are/leadership
"Ms. Ugoretz oversaw intelligence products and briefings for the FBI Director and the Attorney General, as well as FBI analysts’ contributions to the President’s Daily Brief."
Who discovered the Chinese link to HRC's server(s)?
Who reported the discovery?
Who inserted the discovery into the PDB?
Paper-trail.
Q
https://www.dni.gov/index.php/ctiic-who-we-are/leadership
"Ms. Ugoretz oversaw intelligence products and briefings for the FBI Director and the Attorney General, as well as FBI analysts’ contributions to the President’s Daily Brief."
Who discovered the Chinese link to HRC's server(s)?
Who reported the discovery?
Who inserted the discovery into the PDB?
Paper-trail.
Q
Display Options
Delta to next: 0 D_04:24:45 (seconds total: 15885) (27) (9)
Q!!mG7VJxZNCI 08/29/2018 11:23:41 ID: bd309d
8chan/qresearch: 2783126Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Delta to Reply: 0 D_00:01:02 (seconds total: 62) (8) (8)
Epoch: 1535556159 (45) (9)
Anonymous 08/29/2018 11:22:39 ID:6edb2c 8chan/qresearch: 2783116
>>2783065
Q left out the R in server
Q left out the R in server
>>2783116
Error not intended.
Q
Error not intended.
Q
Display Options
Delta to next: 0 D_00:04:24 (seconds total: 264) (12) (3)
Q!!mG7VJxZNCI 08/29/2018 11:19:17 ID: bd309d
8chan/qresearch: 2783065Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Delta to Reply: 0 D_00:03:39 (seconds total: 219) (12) (3)
Epoch: 1535555738 (47) (2)
Q !!mG7VJxZNCI08/29/2018 11:15:38 ID:bd309d 8chan/qresearch: 2783014
http://www.foxnews.com/politics/2018/08/29/chinese-company-reportedly-hacked-clintons-server-got-copy-every-email-in-real-time.html
https://www.reuters.com/article/us-usa-russia-nunes/congressman-nunes-sought-meeting-with-uk-spy-chiefs-in-london-idUSKCN1LD1VX
Q
https://www.reuters.com/article/us-usa-russia-nunes/congressman-nunes-sought-meeting-with-uk-spy-chiefs-in-london-idUSKCN1LD1VX
Q
>>2783014
https://www.nytimes.com/2017/05/20/world/asia/china-cia-spies-espionage.html
Starting in 2010?
HRC Sec of State 2009 - 2013.
Coincidence?
Think Sever Access [granted]
Money talks.
[CROWDSTRIKE]
Q
https://www.nytimes.com/2017/05/20/world/asia/china-cia-spies-espionage.html
Starting in 2010?
HRC Sec of State 2009 - 2013.
Coincidence?
Think Sever Access [granted]
Money talks.
[CROWDSTRIKE]
Q
Display Options
Delta to next: 0 D_00:03:39 (seconds total: 219) (12) (3)
Q!!mG7VJxZNCI 08/29/2018 11:15:38 ID: bd309d
8chan/qresearch: 2783014Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Display Options
Delta to next: 0 D_10:13:00 (seconds total: 36780) (24) (6)
Q!!mG7VJxZNCI 08/29/2018 01:02:38 ID: ea669f
8chan/qresearch: 2779677Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Delta to Reply: 0 D_00:26:30 (seconds total: 1590) (15) (6)
Epoch: 1535517368 (44) (8)
Q !!mG7VJxZNCI08/29/2018 00:36:08 ID:ea669f 8chan/qresearch: 2779165
>>2779059
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
>>2779165
What if a paper-trail exists…
PDB via No Such Agency?
HUSSEIN made aware w/ no action?
Why did POTUS refuse 'select' PDBs during transition?
Who knew?
Threat assessment.
Adm Rogers?
FLYNN?
Why did HUSSEIN + HRC + ADMIN + Staff + … use private emails to communicate?
Was HRC the only one to use unsecured server(s)?
If access was granted re: HRC private server(s) can you assume access was granted re: House server(s) re: AWAN?
AWAN>Pakistani Intelligence?
AWAN FREE?
Huma>Muslim Brotherhood?
Matters of NAT SEC.
Q
What if a paper-trail exists…
PDB via No Such Agency?
HUSSEIN made aware w/ no action?
Why did POTUS refuse 'select' PDBs during transition?
Who knew?
Threat assessment.
Adm Rogers?
FLYNN?
Why did HUSSEIN + HRC + ADMIN + Staff + … use private emails to communicate?
Was HRC the only one to use unsecured server(s)?
If access was granted re: HRC private server(s) can you assume access was granted re: House server(s) re: AWAN?
AWAN>Pakistani Intelligence?
AWAN FREE?
Huma>Muslim Brotherhood?
Matters of NAT SEC.
Q
Display Options
Delta to next: 0 D_00:22:54 (seconds total: 1374) (15) (6)
Q!!mG7VJxZNCI 08/29/2018 00:39:44 ID: ea669f
8chan/qresearch: 2779241Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Delta to Reply: 0 D_00:03:36 (seconds total: 216) (9) (9)
Epoch: 1535517368 (44) (8)
Q !!mG7VJxZNCI08/29/2018 00:36:08 ID:ea669f 8chan/qresearch: 2779165
>>2779059
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
>>2779165
https://www.justice.gov/file/1071991/download
Reconcile.
1 = 1?
1 = 0?
Evidence of an ongoing investigation…..
Q
https://www.justice.gov/file/1071991/download
Reconcile.
1 = 1?
1 = 0?
Evidence of an ongoing investigation…..
Q
Display Options
Delta to next: 0 D_00:03:36 (seconds total: 216) (9) (9)
Q!!mG7VJxZNCI 08/29/2018 00:36:08 ID: ea669f
8chan/qresearch: 2779165Q Clock [ Min: 25 | :25/:55 Mir: 25 | 180 Mir: 55 | :35/:05 Mir: 45 ]
Delta to Reply: 0 D_00:06:38 (seconds total: 398) (20) (2)
Epoch: 1535516970 (42) (6)
Q !!mG7VJxZNCI08/29/2018 00:29:30 ID:ea669f 8chan/qresearch: 2779059
>>2779059
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
Why is POTUS pushing the FBI & DOJ on this issue?
What if access to the server(s) was deliberate?
What if this is 'known' within the intelligence community?
What if this is 'known' within the FBI & DOJ?
If known - why no action?
How might this discredit the FBI's investigation into HRC's emails?
How might this OPEN THE DOOR to [WEINER] / [Huma] / [HRC]?
Logical thinking.
WHY WAS THE INFORMATION ON WEINER'S LAPTOP IN THE FIRST PLACE?
D5.
Q
Display Options
Delta to next: 0 D_05:57:30 (seconds total: 21450) (12) (3)
Q!!mG7VJxZNCI 08/28/2018 18:38:38 ID: b1f9ae
8chan/qresearch: 2772476Q Clock [ Min: 24 | :25/:55 Mir: 26 | 180 Mir: 54 | :35/:05 Mir: 46 ]
Delta to Reply: 0 D_00:01:42 (seconds total: 102) (3) (3)
Epoch: 1535495816 (47) (2)
Anonymous 08/28/2018 18:36:56 ID:ae7506 8chan/qresearch: 2772439
>>2772350
Q,
Relevant yes to the HRC server sweep stakes give away?
https://www.google.com/amp/s/www.nytimes.com/2017/05/20/world/asia/china-cia-spies-espionage.amp.html
Q,
Relevant yes to the HRC server sweep stakes give away?
https://www.google.com/amp/s/www.nytimes.com/2017/05/20/world/asia/china-cia-spies-espionage.amp.html
>>2772439
Display Options
Delta to next: 0 D_00:33:30 (seconds total: 2010) (3) (3)
Q!!mG7VJxZNCI 08/28/2018 18:05:08 ID: 35a7f2
8chan/qresearch: 2771818Q Clock [ Min: 24 | :25/:55 Mir: 26 | 180 Mir: 54 | :35/:05 Mir: 46 ]
Image Name: DWu23teW0AAQy8g.jpg
Filename: a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
EXIF DATA
name : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1042
geometry.height : 786
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 819012
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1042
pageGeometry.height : 786
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : d303baed38d166427b6b9f75595fea78d776ccf23e0e4f306c4587f31e8560e3
profiles.icc :
tainted :
filesize : 74233
numberPixels : 819012
filename : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
name : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1042
geometry.height : 786
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 819012
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1042
pageGeometry.height : 786
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.icc:copyright : Copyright Apple Inc., 2017
properties.icc:description : Display P3
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : d303baed38d166427b6b9f75595fea78d776ccf23e0e4f306c4587f31e8560e3
profiles.icc :
tainted :
filesize : 74233
numberPixels : 819012
filename : a586eea2f55d754ec6b57d42f6326f711cb142df8ddc74542ee7500e07ac37c9.jpg
Image Search Tags:
Trending Non-MSM…
China hacked HRC server?
False.
Access was granted.
You have more than you know.
Q
China hacked HRC server?
False.
Access was granted.
You have more than you know.
Q
Display Options
Delta to next: 13 D_21:42:53 (seconds total: 1201373) (17) (8)
Q!!mG7VJxZNCI 08/14/2018 20:22:15 ID: 0c531f
8chan/qresearch: 2603103Q Clock [ Min: 10 | :25/:55 Mir: 40 | 180 Mir: 40 | :35/:05 Mir: 0 ]
Delta to Reply: 0 D_00:19:30 (seconds total: 1170) (9) (9)
Epoch: 1534291365 (39) (3)
Q !!mG7VJxZNCI08/14/2018 20:02:45 ID:ab9df5 8chan/qresearch: 2602749
GMAIL DRAFTS
[GOOG SAFEGUARDED HIGHEST LEVEL [Access [3-GOOG] - SERVER ROUTING - NON US BASED]
[Sample]
Wet Work?
Human Trafficking?
Sharing of ICE/Border Patrol C-INTEL [schedules] to SAFEGUARD? EXIT/ENTRANCE?
Sharing of FBI C-INTEL to SAFEGUARD PRIV-OPs?
Sharing of DOJ 'Where We Stand' investigation(s) & Guide to OVERCOME-DISMISS-WIN?
Transfer of money instructions to LEFT ORGS>>>DOJ Settlements?
Off-book meetings?
Play dates?
Stand down orders?
Non-action orders?
Muslim Brotherhood?
Cross coord w/ UK assets / O-PRO in SIS/UK-P?
Coord w/ foreign actors for payment/money disperse?
Coord w/ AID ORGS for [illegal] plans?
HAM radio instructions if remote-5?
……………..
Why did ES make public NSA CLAS tools?
Think XKeyscore + PRISM specifically.
Was such tech kept from 'elected' officials?
Was such tech kept from 'elected' directors?
Why was NO SUCH AGENCY created?
Think SIGINT.
What ADVANTAGES exist to BIG TECH, other ABC off/on agencies, elected officials, CEOs, FOREIGN ADVERSARIES etc. if such information is learned?
What price are you (the PUBLIC) willing to pay?
Did you ever play HIDE-AND-SEEK?
Q
[GOOG SAFEGUARDED HIGHEST LEVEL [Access [3-GOOG] - SERVER ROUTING - NON US BASED]
[Sample]
Wet Work?
Human Trafficking?
Sharing of ICE/Border Patrol C-INTEL [schedules] to SAFEGUARD? EXIT/ENTRANCE?
Sharing of FBI C-INTEL to SAFEGUARD PRIV-OPs?
Sharing of DOJ 'Where We Stand' investigation(s) & Guide to OVERCOME-DISMISS-WIN?
Transfer of money instructions to LEFT ORGS>>>DOJ Settlements?
Off-book meetings?
Play dates?
Stand down orders?
Non-action orders?
Muslim Brotherhood?
Cross coord w/ UK assets / O-PRO in SIS/UK-P?
Coord w/ foreign actors for payment/money disperse?
Coord w/ AID ORGS for [illegal] plans?
HAM radio instructions if remote-5?
……………..
Why did ES make public NSA CLAS tools?
Think XKeyscore + PRISM specifically.
Was such tech kept from 'elected' officials?
Was such tech kept from 'elected' directors?
Why was NO SUCH AGENCY created?
Think SIGINT.
What ADVANTAGES exist to BIG TECH, other ABC off/on agencies, elected officials, CEOs, FOREIGN ADVERSARIES etc. if such information is learned?
What price are you (the PUBLIC) willing to pay?
Did you ever play HIDE-AND-SEEK?
Q
>>2602749
https://apnews.com/828aefab64d4411bac257a07c1af0ecb/AP-Exclusive:-Google-tracks-your-movements,-like-it-or-not
[SIRI]
FB listens [even after you remove app].
TWITTER GEO-T/L
You are under constant tracking/surveillance.
DARPA.
Q
https://apnews.com/828aefab64d4411bac257a07c1af0ecb/AP-Exclusive:-Google-tracks-your-movements,-like-it-or-not
[SIRI]
FB listens [even after you remove app].
TWITTER GEO-T/L
You are under constant tracking/surveillance.
DARPA.
Q
Display Options
Delta to next: 0 D_00:19:30 (seconds total: 1170) (9) (9)
Q!!mG7VJxZNCI 08/14/2018 20:02:45 ID: ab9df5
8chan/qresearch: 2602749Q Clock [ Min: 10 | :25/:55 Mir: 40 | 180 Mir: 40 | :35/:05 Mir: 0 ]
GMAIL DRAFTS
[GOOG SAFEGUARDED HIGHEST LEVEL [Access [3-GOOG] - SERVER ROUTING - NON US BASED]
[Sample]
Wet Work?
Human Trafficking?
Sharing of ICE/Border Patrol C-INTEL [schedules] to SAFEGUARD? EXIT/ENTRANCE?
Sharing of FBI C-INTEL to SAFEGUARD PRIV-OPs?
Sharing of DOJ 'Where We Stand' investigation(s) & Guide to OVERCOME-DISMISS-WIN?
Transfer of money instructions to LEFT ORGS>>>DOJ Settlements?
Off-book meetings?
Play dates?
Stand down orders?
Non-action orders?
Muslim Brotherhood?
Cross coord w/ UK assets / O-PRO in SIS/UK-P?
Coord w/ foreign actors for payment/money disperse?
Coord w/ AID ORGS for [illegal] plans?
HAM radio instructions if remote-5?
……………..
Why did ES make public NSA CLAS tools?
Think XKeyscore + PRISM specifically.
Was such tech kept from 'elected' officials?
Was such tech kept from 'elected' directors?
Why was NO SUCH AGENCY created?
Think SIGINT.
What ADVANTAGES exist to BIG TECH, other ABC off/on agencies, elected officials, CEOs, FOREIGN ADVERSARIES etc. if such information is learned?
What price are you (the PUBLIC) willing to pay?
Did you ever play HIDE-AND-SEEK?
Q
[GOOG SAFEGUARDED HIGHEST LEVEL [Access [3-GOOG] - SERVER ROUTING - NON US BASED]
[Sample]
Wet Work?
Human Trafficking?
Sharing of ICE/Border Patrol C-INTEL [schedules] to SAFEGUARD? EXIT/ENTRANCE?
Sharing of FBI C-INTEL to SAFEGUARD PRIV-OPs?
Sharing of DOJ 'Where We Stand' investigation(s) & Guide to OVERCOME-DISMISS-WIN?
Transfer of money instructions to LEFT ORGS>>>DOJ Settlements?
Off-book meetings?
Play dates?
Stand down orders?
Non-action orders?
Muslim Brotherhood?
Cross coord w/ UK assets / O-PRO in SIS/UK-P?
Coord w/ foreign actors for payment/money disperse?
Coord w/ AID ORGS for [illegal] plans?
HAM radio instructions if remote-5?
……………..
Why did ES make public NSA CLAS tools?
Think XKeyscore + PRISM specifically.
Was such tech kept from 'elected' officials?
Was such tech kept from 'elected' directors?
Why was NO SUCH AGENCY created?
Think SIGINT.
What ADVANTAGES exist to BIG TECH, other ABC off/on agencies, elected officials, CEOs, FOREIGN ADVERSARIES etc. if such information is learned?
What price are you (the PUBLIC) willing to pay?
Did you ever play HIDE-AND-SEEK?
Q
Display Options
Delta to next: 3 D_06:50:14 (seconds total: 283814) (26) (8)
Q!!mG7VJxZNCI 08/11/2018 13:12:31 ID:
8chan/patriotsfight: 139Q Clock [ Min: 7 | :25/:55 Mir: 43 | 180 Mir: 37 | :35/:05 Mir: 3 ]
These people are stupid!
https://www.cohenmilsteinprocessserver.com
"Never Interfere With an Enemy While He’s in the Process of Destroying Himself."
Discovery.
http://thehill.com/policy/cybersecurity/400882-wikileaks-says-senate-panel-requested-assange-testimony-in-russia-probe
Do you believe in coincidences?
We have the source.
Q
https://www.cohenmilsteinprocessserver.com
"Never Interfere With an Enemy While He’s in the Process of Destroying Himself."
Discovery.
http://thehill.com/policy/cybersecurity/400882-wikileaks-says-senate-panel-requested-assange-testimony-in-russia-probe
Do you believe in coincidences?
We have the source.
Q
Display Options
Delta to next: 7 D_19:46:02 (seconds total: 675962) (35) (8)
Q!CbboFOtcZs 08/03/2018 17:26:29 ID:
8chan/patriotsfight: 117Q Clock [ Min: 59 | :25/:55 Mir: 51 | 180 Mir: 29 | :35/:05 Mir: 11 ]
Display Options
Delta to next: 8 D_21:29:51 (seconds total: 768591) (36) (9)
Q!CbboFOtcZs 07/25/2018 19:56:38 ID: 77016b
8chan/qresearch: 2287674Q Clock [ Min: 50 | :25/:55 Mir: 0 | 180 Mir: 20 | :35/:05 Mir: 20 ]
Delta to Reply: 0 D_00:18:04 (seconds total: 1084) (13) (4)
Epoch: 1532561914 (37) (1)
Q !CbboFOtcZs07/25/2018 19:38:34 ID:77016b 8chan/qresearch: 2287348
>>2287225
When did No Name travel to the UK?
Q
When did No Name travel to the UK?
Q
Delta to Reply: 0 D_00:18:04 (seconds total: 1084) (13) (4)
Epoch: 1532561914 (37) (1)
Q !CbboFOtcZs07/25/2018 19:38:34 ID:77016b 8chan/qresearch: 2287348
>>2287225
When did No Name travel to the UK?
Q
>>2287348
>>2287348
What if the UK gov worked hand-in-hand w/ the Hussein admin to sabotage the 2016 election?
Data collection.
Voice.
Video.
Bugging.
Creation of fake intel dossier using ex spy.
Co-sponsor insurance policy re: POTUS election.
PS.
LP.
No Name.
Clapper.
Brennan.
Rice.
LL.
HRC.
BC.
Hussein.
+22
What if intel masked penetration(s) to frame Russia?
Crowdstrike?
Servers.
SR.
JA.
Why does the UK gov desperately want JA?
Think source files.
The more you know.
Q
>>2287348
What if the UK gov worked hand-in-hand w/ the Hussein admin to sabotage the 2016 election?
Data collection.
Voice.
Video.
Bugging.
Creation of fake intel dossier using ex spy.
Co-sponsor insurance policy re: POTUS election.
PS.
LP.
No Name.
Clapper.
Brennan.
Rice.
LL.
HRC.
BC.
Hussein.
+22
What if intel masked penetration(s) to frame Russia?
Crowdstrike?
Servers.
SR.
JA.
Why does the UK gov desperately want JA?
Think source files.
The more you know.
Q
Display Options
Delta to next: 1 D_08:11:11 (seconds total: 115871) (23) (5)
Q!CbboFOtcZs 07/24/2018 11:45:27 ID: 5b7dc4
8chan/qresearch: 2262557Q Clock [ Min: 49 | :25/:55 Mir: 1 | 180 Mir: 19 | :35/:05 Mir: 21 ]
From Sea to Shining Sea.
Who does Huber report to [directly]?
Define evidence.
Who has the server?
Why does POTUS continually refer to the server?
POTUS does not speculate.
Future proves past.
Who has it all?
Topics stated in past.
Future BIG meaning?
Repeats important.
Think Twitter.
Those awake see.
Those asleep blind.
Fake news [prop arm of D/DS] failing.
Panic.
Silence is golden.
Q
Who does Huber report to [directly]?
Define evidence.
Who has the server?
Why does POTUS continually refer to the server?
POTUS does not speculate.
Future proves past.
Who has it all?
Topics stated in past.
Future BIG meaning?
Repeats important.
Think Twitter.
Those awake see.
Those asleep blind.
Fake news [prop arm of D/DS] failing.
Panic.
Silence is golden.
Q
Display Options
Delta to next: 21 D_09:47:12 (seconds total: 1849632) (33) (6)
Q!CbboFOtcZs 07/03/2018 01:58:15 ID: e429ce
8chan/qresearch: 2007973Q Clock [ Min: 28 | :25/:55 Mir: 22 | 180 Mir: 58 | :35/:05 Mir: 42 ]
Delta to Reply: 0 D_00:05:31 (seconds total: 331) (7) (7)
Epoch: 1530597164 (41) (5)
Q !CbboFOtcZs07/03/2018 01:52:44 ID:e429ce 8chan/qresearch: 2007869
https://www.breitbart.com/big-government/2018/07/02/nunes-refers-ten-obama-officials-to-house-judiciary-and-oversight-joint-task-force/amp/?__twitter_impression=true
Re_ read drops re: Five Eyes / FVEY.
Will be extremely important going forward.
[UK] - primary
Turn taken.
FBI/DOJ to State / Hussein WH (inc C_A / other appointment Start) to Foreign Bad Actors.
[RR] deadline?
We have the server.
Q
Re_ read drops re: Five Eyes / FVEY.
Will be extremely important going forward.
[UK] - primary
Turn taken.
FBI/DOJ to State / Hussein WH (inc C_A / other appointment Start) to Foreign Bad Actors.
[RR] deadline?
We have the server.
Q
Delta to Reply: 0 D_00:03:16 (seconds total: 196) (16) (7)
Epoch: 1530597299 (50) (5)
Q !CbboFOtcZs07/03/2018 01:54:59 ID:e429ce 8chan/qresearch: 2007911
>>2007869
“Normally, intelligence passed on from a member of the “Five Eyes” alliance — Australia, Canada, New Zealand, the U.K., and the U.S. — to another member comes through an official channel for intelligence sharing.
However, Nunes, upon reviewing the document that formally launched the FBI’s investigation, said there was no intelligence shared through that official channel, meaning that the intelligence was shared through unofficial means.”
Q
Image Name: 4EBD68A2-4F6C-4EDF-894D-BF19CFC21B08.jpeg
Filename: e7a0e7d7afd132d1f29611581bbf3e21899426cdf52af89ef20ed2e93ccb77ad.jpeg
EXIF DATA
name : e7a0e7d7afd132d1f29611581bbf3e21899426cdf52af89ef20ed2e93ccb77ad.jpeg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1200
geometry.height : 670
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 804000
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1200
pageGeometry.height : 670
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 384fa8e20a511a6f912193d75c66dcb935ad4dd814c6d9247a1f4901e15861ec
tainted :
filesize : 102723
numberPixels : 804000
filename : e7a0e7d7afd132d1f29611581bbf3e21899426cdf52af89ef20ed2e93ccb77ad.jpeg
name : e7a0e7d7afd132d1f29611581bbf3e21899426cdf52af89ef20ed2e93ccb77ad.jpeg
format : JPEG
formatDescription : Joint Photographic Experts Group JFIF format
mimeType : image/jpeg
class : DirectClass
geometry.width : 1200
geometry.height : 670
geometry.x : 0
geometry.y : 0
units : Undefined
type : TrueColor
endianess : Undefined
colorspace : sRGB
depth : 8
baseDepth : 8
channelDepth.red : 8
channelDepth.green : 8
channelDepth.blue : 8
pixels : 804000
renderingIntent : Perceptual
gamma : 0.454545
backgroundColor : #FFFFFF
borderColor : #DFDFDF
matteColor : #BDBDBD
transparentColor : #000000
interlace : JPEG
intensity : Undefined
compose : Over
pageGeometry.width : 1200
pageGeometry.height : 670
pageGeometry.x : 0
pageGeometry.y : 0
dispose : Undefined
iterations : 0
compression : JPEG
quality : 85
orientation : Undefined
properties.jpeg:colorspace : 2
properties.jpeg:sampling-factor : 2x2,1x1,1x1
properties.signature : 384fa8e20a511a6f912193d75c66dcb935ad4dd814c6d9247a1f4901e15861ec
tainted :
filesize : 102723
numberPixels : 804000
filename : e7a0e7d7afd132d1f29611581bbf3e21899426cdf52af89ef20ed2e93ccb77ad.jpeg
Image Search Tags:
>>2007869
>>2007911
>>2007911
Display Options
Delta to next: 0 D_00:03:16 (seconds total: 196) (16) (7)
Q!CbboFOtcZs 07/03/2018 01:54:59 ID: e429ce
8chan/qresearch: 2007911Q Clock [ Min: 28 | :25/:55 Mir: 22 | 180 Mir: 58 | :35/:05 Mir: 42 ]
Delta to Reply: 0 D_00:02:15 (seconds total: 135) (9) (9)
Epoch: 1530597164 (41) (5)
Q !CbboFOtcZs07/03/2018 01:52:44 ID:e429ce 8chan/qresearch: 2007869
https://www.breitbart.com/big-government/2018/07/02/nunes-refers-ten-obama-officials-to-house-judiciary-and-oversight-joint-task-force/amp/?__twitter_impression=true
Re_ read drops re: Five Eyes / FVEY.
Will be extremely important going forward.
[UK] - primary
Turn taken.
FBI/DOJ to State / Hussein WH (inc C_A / other appointment Start) to Foreign Bad Actors.
[RR] deadline?
We have the server.
Q
Re_ read drops re: Five Eyes / FVEY.
Will be extremely important going forward.
[UK] - primary
Turn taken.
FBI/DOJ to State / Hussein WH (inc C_A / other appointment Start) to Foreign Bad Actors.
[RR] deadline?
We have the server.
Q
>>2007869
“Normally, intelligence passed on from a member of the “Five Eyes” alliance — Australia, Canada, New Zealand, the U.K., and the U.S. — to another member comes through an official channel for intelligence sharing.
However, Nunes, upon reviewing the document that formally launched the FBI’s investigation, said there was no intelligence shared through that official channel, meaning that the intelligence was shared through unofficial means.”
Q
“Normally, intelligence passed on from a member of the “Five Eyes” alliance — Australia, Canada, New Zealand, the U.K., and the U.S. — to another member comes through an official channel for intelligence sharing.
However, Nunes, upon reviewing the document that formally launched the FBI’s investigation, said there was no intelligence shared through that official channel, meaning that the intelligence was shared through unofficial means.”
Q